Blogs
Stay updated with the latest articles on technology, security, and digital transformation—designed to inform and inspire your business growth.
-
Blog25 May 2021Microsoft Email Users Fall Prey to FedEx Phishing EmailsMicrosoft email users seem to be repeatedly be targeted by one phishing...
-
Blog21 May 2021Celsius Data Breach – Phishing Claims More VictimsCelsius, a crypto lending service, recently learned of a security break at...
-
Blog20 May 2021Ransomware Attack At Realty Firm– Possible Data LossA realty firm called Ansal Housing recently fell prey to a ransomware...
-
Blog12 May 2021Banking Customers Fall Prey to Phishing ScamsSensitive banking information is always a matter of great anxiety for us...
-
Blog10 May 2021Exchange Email HackThe Rampage Continues Vulnerabilities in a major player’s server architecture is an...
-
Blog29 April 2021Growing Concerns of Credential Theft CasesDeep research into cyber security threat patterns has revealed some trends in...
-
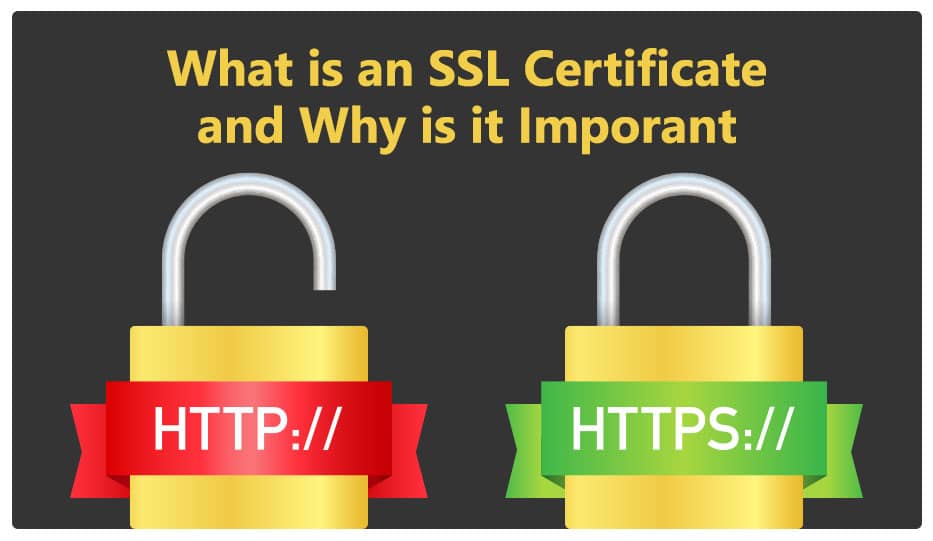
Blog26 April 2021What is an SSL Certificate and why is it important?Why worry about an SSL Certificate? There are a lot of little...
-
Blog22 April 2021EU Banking Regulator Victimized by Microsoft Email HackMajor Financial Institution Compromised The European Banking Authority, one of the foremost...
-
Blog20 April 20214 New Hacker Groups Target Microsoft Email ServersAfter the focused attacks on Microsoft email servers by alleged state-sponsored hacking...
-
Blog14 April 2021Microsoft Exchange Server Flaws Affect 30,000 CompaniesA slow-burn cyber breach has been transpiring since January, only recently coming...
-
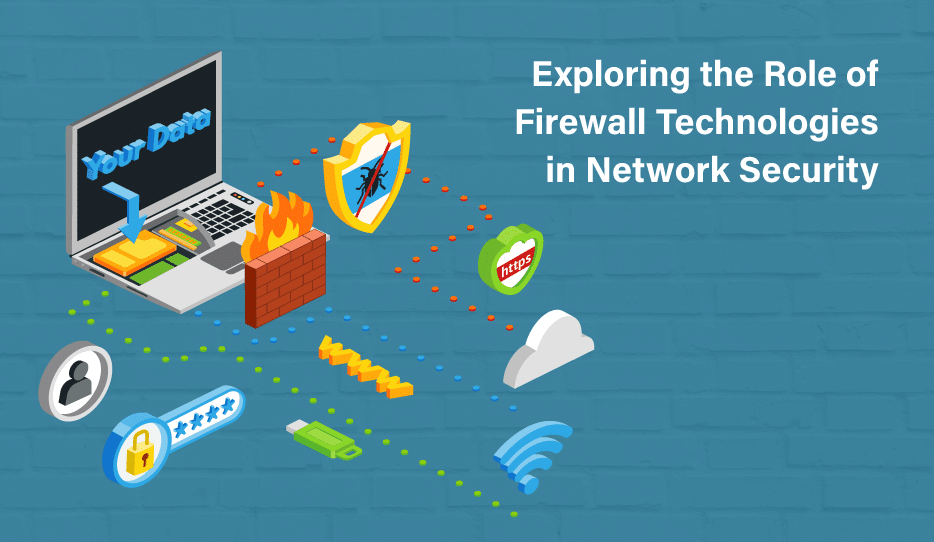
Exploring the Role of Firewall Technologies in Network Security
Understanding the need for firewall technologies In today's interconnected world, network security...
-
SMTP Security and Authentication
In today's digitally interconnected world, email has become an indispensable means of...
-
Fortinet Ransomware Protection Survey
In today's interconnected digital landscape, organizations face a persistent and growing threat...
-
Barracuda Zero-Day Exploit
In a shocking revelation, cybersecurity researchers have discovered that a zero-day vulnerability...
-
Benefits of DMARC for Email Domain Protection
In today's digital landscape, email has become an integral part of our...
-
Improving your cyber security strength
The percentage of companies globally ranked as mature in device security is...
-
Blog 17 August 2023 3 Ways Microsoft Teams Phone Boosts Workplace Productivity -
Blog 17 August 2023 Cyber Security for Financial Institutions -
Blog 14 August 2023 AI Email Security to Combat AI Email Threats -
Blog 11 August 2023 Mahesh Bank Cyber Incident – ₹65 Lakh Penalty for Lapses in Cybersecurity -
Blog 28 July 2023 Logix Opens Doors for White Label Partnerships in Email Security and Collaboration Solutions -
Blog 20 July 2023 Additional security for Office 365
-
3 Ways Microsoft Teams Phone Boosts Workplace ProductivityVoice communication is a crucial element in business that plays a vital...
-
Cyber Security for Financial InstitutionsThe scope of cyber security for financial institutions has expanded in recent...
-
AI Email Security to Combat AI Email ThreatsIn the rapidly evolving landscape of 2023, Artificial Intelligence (AI) has emerged...
-
Mahesh Bank Cyber Incident – ₹65 Lakh Penalty for Lapses in CybersecurityThe Mahesh Bank cyber incident was a shocking episode for banks across...
-
Logix Opens Doors for White Label Partnerships in Email Security and Collaboration SolutionsLogix, a leading provider of email security and collaboration solution has announced...
-
Additional security for Office 365Do you need additional security for Office 365? When users deal with...