Blogs
Stay updated with the latest articles on technology, security, and digital transformation—designed to inform and inspire your business growth.
-
Blog6 April 2021Hackers Target Government Officials Through Rogue Email IDSeveral officials in the government were targeted for phishing through a rogue...
-
Blog2 April 2021Getting a bonus is always good… unless it’s an advanced Bazar Trojan in disguiseSecurity researchers have found a deadly variant of a Bazar Trojan that...
-
Blog30 March 2021Hosting Provider Phishing ScamCyber criminals will often use scare tactics to prod their victims into...
-
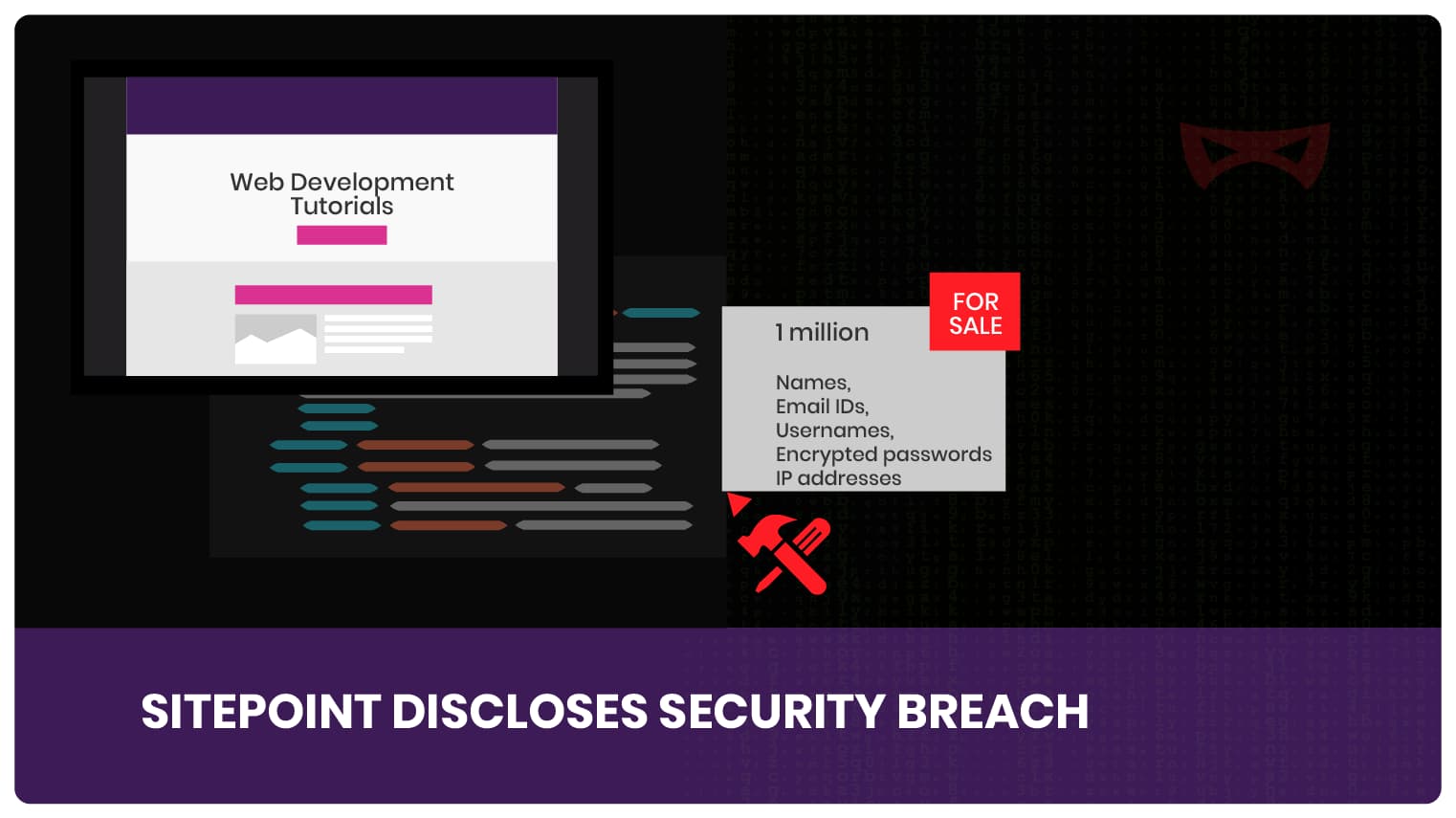
Blog16 March 2021SitePoint Security BreachSitePoint is an online portal which provides some great tutorials on web...
-
Blog15 March 2021Office365 Email Compromise – SolarWinds Faces Security BreachSolarWinds, an IT services company, recently faced issue with their email security....
-
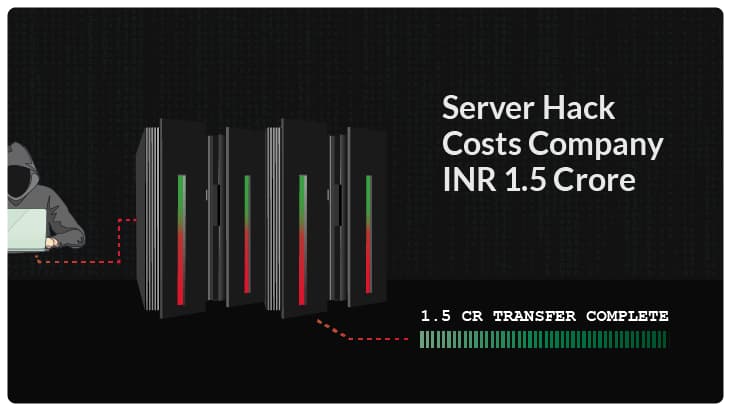
Blog12 March 2021Server Hack Costs 1.5 Crore in LossesCase Specifics A private company based in Pune recently suffered from a...
-
Blog9 March 2021Malwarebytes Hacked by The Same Group Behind SolarWinds Security BreachCyber security firm themselves are lucrative targets for hackers. It is a...
-
Blog5 March 2021Common Cyber Attacks You Should KnowIt is true that most common cyber attacks leverage gaps in technical...
-
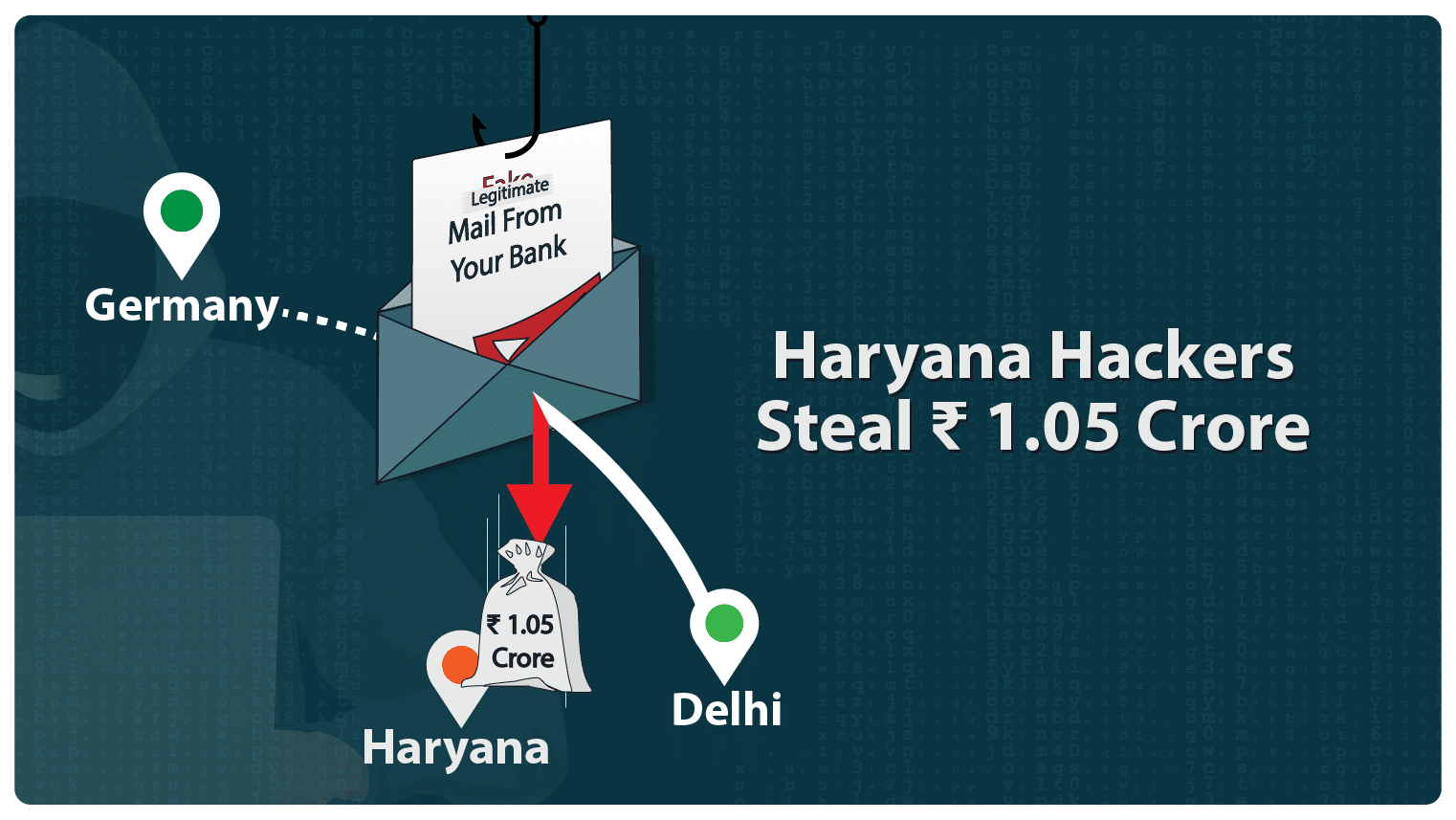
Blog25 February 2021Haryana Hackers Steal INR 1 CroreHaryana hackers defrauded ISGEC Heavy Engineering company and nicked an amount of...
-
Blog18 February 2021Microsoft Fails to Block O365 Email Spoofing AttacksMicrosoft is under the gun again for cyber fraud. 200 million+ users...
-
How Deepfake is risky
What is deep fake? Deepfake has gained wide accessibility and popularity. Deepfake...
-
How VolumeMail SMTP Can Improve Your Business Email Marketing Strategy
Email marketing is a powerful tool for businesses of all sizes, allowing...
-
How to Improve Your Email Deliverability with BIMI
Email marketing is a crucial aspect of any business's strategy. However, with...
-
Why Regular Web Security Assessments Are Critical for Your Business
Cyber security threats are becoming increasingly sophisticated, making it more challenging for...
-
4 Ways to Spot and Avoid Phishing Scams
Phishing scams are a widespread problem in today's digital age. Criminals use...
-
Microsoft 365 for work efficiency
As the world continues to grapple with the effects of the COVID-19...
-
Blog 20 July 2023 The Role of DMARC In Combatting BEC Attacks -
Blog 20 July 2023 ION Group Ransomware Attack -
Blog 18 July 2023 BlackCat Ransomware Group Exploits WinSCP in Malvertising Campaigns Targeting Corporate Networks -
Blog 20 June 2023 4 Effective Email Marketing Campaigns for Small Businesses -
Blog 8 June 2023 Understanding Simulated Phishing Campaigns with 5 Easy Steps -
Blog 8 June 2023 Top 10 Open Source Software Threats
-
The Role of DMARC In Combatting BEC AttacksLiving in today’s world, it is extremely likely you have been using...
-
ION Group Ransomware AttackLockBit ransomware strikes again ION Group, a software company located in the...
-
BlackCat Ransomware Group Exploits WinSCP in Malvertising Campaigns Targeting Corporate NetworksIn a concerning development, researchers at a leading Cyber Security firm have...
-
4 Effective Email Marketing Campaigns for Small BusinessesEmail marketing campaigns have proved to be the most ROI-positive marketing tools...
-
Understanding Simulated Phishing Campaigns with 5 Easy StepsSimulated phishing campaigns to combat social engineering Phishing simulation is your tool...
-
Top 10 Open Source Software ThreatsSoftware supply chains have been exploited more and more in the recent...