Blogs
Stay updated with the latest articles on technology, security, and digital transformation—designed to inform and inspire your business growth.
-
Blog15 April 2020Newsletter from Reserve Bank Information Technology Private Limited (ReBIT) on CybersecurityAn article shared by Mr. Nandkumar Saravade, CEO, ReBIT in Cyber Pulse...
-
Blog13 April 2020You’ve Won An Award: Is It Really Just Good News In That Celebratory Email?Congratulations! You have won … a free phishing scam! Everybody loves to...
-
Blog11 April 2020Tree Sena: An Unfortunate Cybercrime Case That Affected A Noble CauseTree Sena: A Sad Case of Identity Theft The scenario revolving around...
-
Blog6 April 2020Watch Out! Public Health Group Officials Being Imitated For Phishing CampaignsPublic Health Group Officials Imitated for Sending Out Phishing Emails We have...
-
Blog3 April 2020Corporate Email Eavesdropping: Is Someone Spying On You?A Mysterious Hacker Group Has Been Spying on Corporate Email and FTP...
-
Blog2 April 2020The Google Calendar Spam: Something you need to know?Google Calendar Falls Prey to Spammers A rather unique spamming technique has...
-
Blog26 March 2020Multi-Factor Authentication: The Devil Is In The DetailsHackers attacked more than a million Microsoft Accounts ! If you need...
-
Blog23 March 2020Coronavirus Sparks A Series of Phishing RusesCurb your instincts; don’t open emails just because they claim to contain...
-
Blog17 March 2020Coronavirus Forces Employees to Work From Home. But What About Remote Security?Covid-19 Outbreak forcing you to work from home? Here are the best...
-
Blog13 March 2020Microsoft Office 365 and Google G Suite Become Hot Targets for BECFBI Reports Suggest BEC should be treated as seriously as Ransomware For...
-
ION Group Ransomware Attack
LockBit ransomware strikes again ION Group, a software company located in the...
-
BlackCat Ransomware Group Exploits WinSCP in Malvertising Campaigns Targeting Corporate Networks
In a concerning development, researchers at a leading Cyber Security firm have...
-
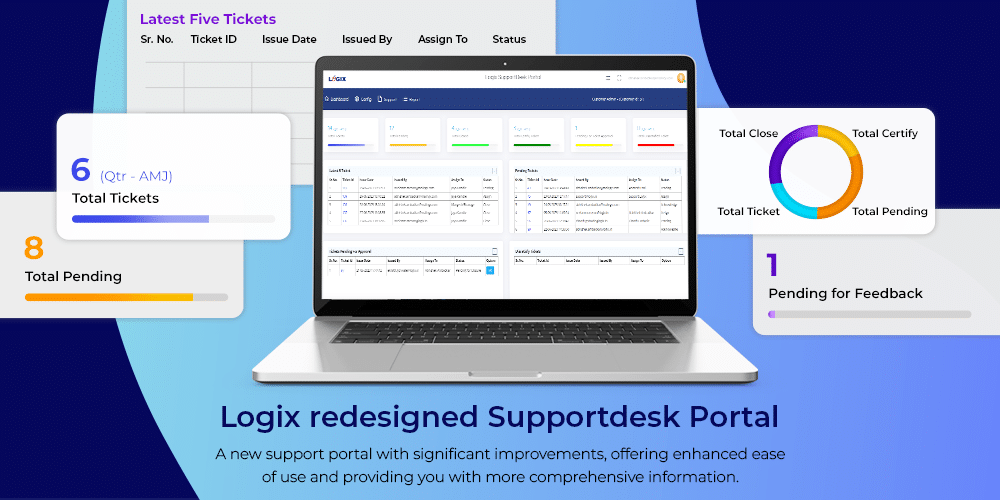
Introducing the Revamped Logix SupportDesk Portal
We are thrilled to announce our newly redesigned Logix Supportdesk portal is...
-
4 Effective Email Marketing Campaigns for Small Businesses
Email marketing campaigns have proved to be the most ROI-positive marketing tools...
-
Understanding Simulated Phishing Campaigns with 5 Easy Steps
Simulated phishing campaigns to combat social engineering Phishing simulation is your tool...
-
Top 10 Open Source Software Threats
Software supply chains have been exploited more and more in the recent...
-
Blog 25 November 2022 Securing hybrid IT environments -
Blog 20 October 2022 Microsoft Shuts Down Exchange Online Basic Authentication Services -
Blog 18 October 2022 Deprecation of Microsoft Basic Authentication for Exchange Online -
Blog 18 October 2022 Celebrating Safety this National Cybersecurity Awareness Month (NCSAM 2022) -
Blog 12 July 2022 How Zimbra Collaboration Tool Revamped During the Pivotal Pandemic Stage -
Blog 5 July 2022 How Digital Transformation has become a necessity for businesses
-
Securing hybrid IT environmentsWhen cloud technologies had first emerged, several businesses had jumped on the...
-
Microsoft Shuts Down Exchange Online Basic Authentication ServicesAs cyber-attacks continue targeting remote workers and hybrid environments, Microsoft is taking...
-
Deprecation of Microsoft Basic Authentication for Exchange OnlineUntil recently, the industry has relied on basic authentication as a security...
-
Celebrating Safety this National Cybersecurity Awareness Month (NCSAM 2022)Every year, October is observed as National Cybersecurity Awareness Month. During this...
-
How Zimbra Collaboration Tool Revamped During the Pivotal Pandemic StageThe Covid-19 pandemic seems to be receding in impact but back when...
-
How Digital Transformation has become a necessity for businessesOver the past couple of years, businesses have absolutely had to evolve...