Blogs
Stay updated with the latest articles on technology, security, and digital transformation—designed to inform and inspire your business growth.
-
Blog3 July 2018Emotet Malware spreading extensively via Microsoft Documents in emailsHackers are trying to deliver Emotet malware by attaching it to Microsoft...
-
Blog30 June 2018Cloud Technology has brought in a paradigm shift in Storing DataCloud Computing has flourished enormously over the past few years. It has...
-
Blog27 June 2018Indian BFSI Sector needs to be prepared for upcoming data protection lawsThe increase in financial crimes is not only a threat to BFSI...
-
Blog17 June 2018What is DMARC? Why is it important for your business?What is DMARC? DMARC (Domain-based Message Authentication, Reporting and Conformance) is a...
-
Blog15 June 2018Bypass glitch makes Mac OS vulnerable due to improper code-signing implementationA bypass found in third party developers’ interpretation of code signing API...
-
Blog13 June 2018Beware of this Top 10 most misused DomainsIn the latest research it is revealed that, some of the latest...
-
Blog6 June 2018Stay protected from Domain Spoofing – Know all about it!What is spoofing? Cyber criminal can easily impersonate or forges domains, IP...
-
Blog3 June 2018How to differentiate rogue URLs from the authentic onesHow can you identify if the domain is authentic or impostor? The...
-
Blog31 May 2018Why Blockchain may not be the elixir to internet securityEvery architect, builder and designer knows that the right tool can solve...
-
Cyber Security Advisory – Apache Log4J Remote Code Execution Vulnerability (CVE-2021-44228
Log4Shell: RCE 0-day exploit found in log4j2, a popular Java logging package....
-
Do your best work with Microsoft 365 Solutions
Microsoft 365 is here to provide the best integrate experience for your...
-
Russian threat group after 14,000 Gmail accounts
A Russian-linked hacker group, APT28, purported to have been on a month-long...
-
The 7 worst data breaches of 2021
Because every business is now online, it generates plenty more data than...
-
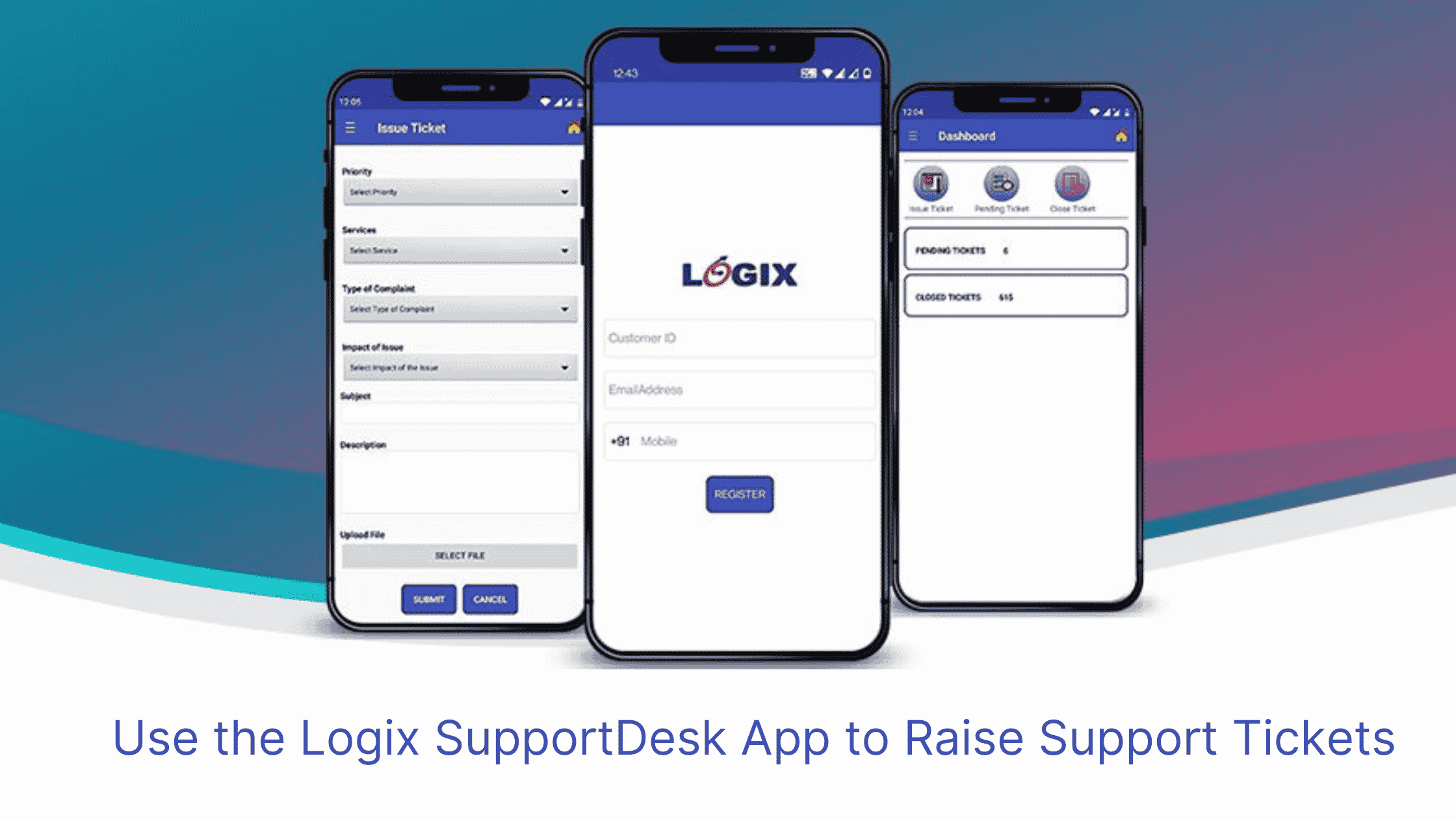
Now use the Logix SupportDesk App to Raise Support Tickets
When was the last time you spent a day without your phone?...
-
Ransomware trends in 2021
Ransomware attacks have been on a steady rise in 2021, both in number of ransomware attacks and also...
-
Blog 15 March 2021 Office365 Email Compromise – SolarWinds Faces Security Breach -
Blog 12 March 2021 Server Hack Costs 1.5 Crore in Losses -
Blog 9 March 2021 Malwarebytes Hacked by The Same Group Behind SolarWinds Security Breach -
Blog 5 March 2021 Common Cyber Attacks You Should Know -
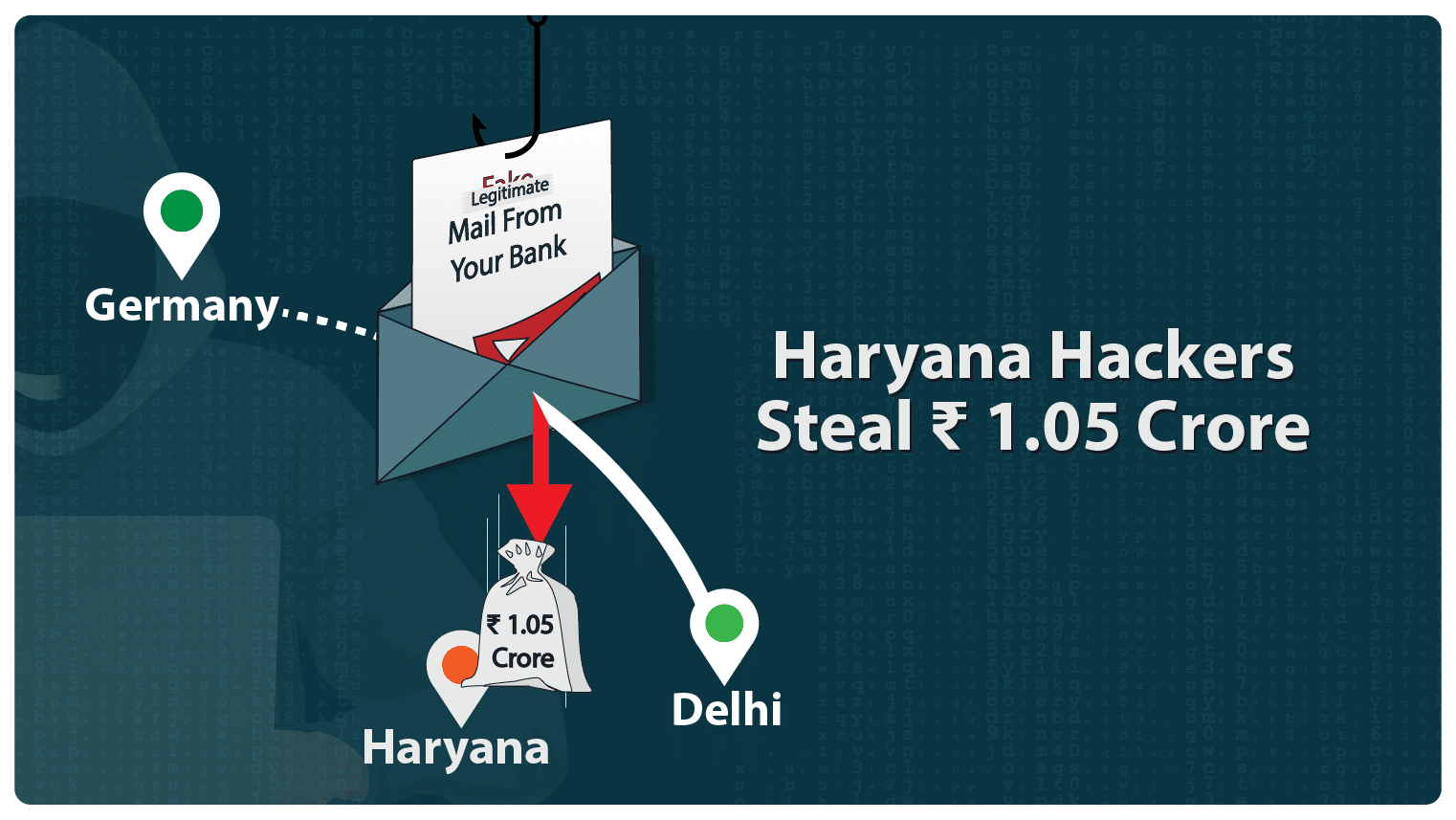
Blog 25 February 2021 Haryana Hackers Steal INR 1 Crore -
Blog 18 February 2021 Microsoft Fails to Block O365 Email Spoofing Attacks
-
Office365 Email Compromise – SolarWinds Faces Security BreachSolarWinds, an IT services company, recently faced issue with their email security....
-
Server Hack Costs 1.5 Crore in LossesCase Specifics A private company based in Pune recently suffered from a...
-
Malwarebytes Hacked by The Same Group Behind SolarWinds Security BreachCyber security firm themselves are lucrative targets for hackers. It is a...
-
Common Cyber Attacks You Should KnowIt is true that most common cyber attacks leverage gaps in technical...
-
Haryana Hackers Steal INR 1 CroreHaryana hackers defrauded ISGEC Heavy Engineering company and nicked an amount of...
-
Microsoft Fails to Block O365 Email Spoofing AttacksMicrosoft is under the gun again for cyber fraud. 200 million+ users...