Blogs
Stay updated with the latest articles on technology, security, and digital transformation—designed to inform and inspire your business growth.
-
Blog9 April 2018Latest technology innovations affecting cyber securityTechnology is building our future, there is no denying but with every...
-
Blog2 April 2018Preventive measures for the growing DDoS AttacksDDoS(Denial of Distributed Service) attack is a type of cyber attack that...
-
Blog2 April 2018How cloud is influencing the roles and responsibilities of CIO?Cloud has had a gigantic effect on the software industry. And its...
-
Blog2 April 2018With the increasing third party leaks, Aadhar Card systems need security reviewsAadhar Card database is by far one of the largest government databases...
-
-
Blog26 March 2018How CIO can spread cyber security awareness among the employeesCyber security hacks and breaches have become more widespread and are more...
-
Blog26 March 2018Critical takeaways for CIOs from the 2017 cyber crimes!Cyber security of an organization has evolved dramatically over the last decade....
-
Blog26 March 2018Cloud based security and analytics is the key to network protectionCloud based security and analytics is a service model in which a...
-
Blog26 March 2018Hacked email? Things you must doSo, your email has been hacked! Well this is very likely in...
-
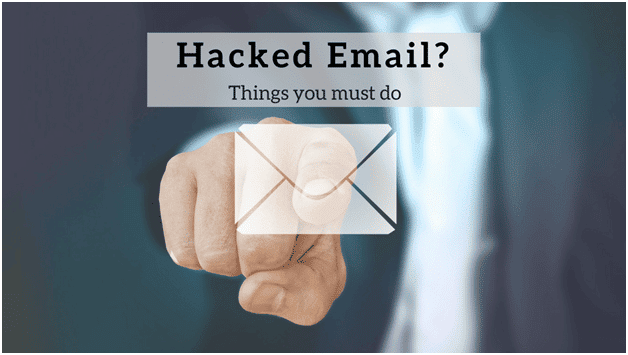
Logix InfoSecurity Receives the 2021 Ingram Micro Cloud Partner Award
Ingram Micro Cloud honors Logix InfoSecurity Pvt. Ltd for its ability to...
-
Update for Logix Cloud Email ATP customers
We recently upgraded our email security functionality with new enhancements for our...
-
4 data protection tools for your small business
Any business today generates heaps of data, a majority of which is...
-
Benefits of Zoom for small businesses
Zoom offers the most features for remote collaboration, at the most feasible...
-
Microsoft 365 Security in the Cloud
Along with dependable protection, Microsoft 365 Security solutions now bring a much-needed...
-
Accenture in the crosshairs of Lockbit ransomware attack
A well-known consulting firm, Accenture, has fallen prey to a ransomware attack...
-
Blog 23 October 2020 These two companies are favourites for spoofed emails -
Blog 18 October 2020 Business Email Compromise: A Complete Guide -
Blog 10 October 2020 Why Web Application Firewall Is a Must In Your Security Arsenal -
Blog 7 October 2020 Credentials Theft: A Case Study -
Blog 23 September 2020 Major Data Breach of Government Computers -
Blog 8 September 2020 Look out for Covid-19 Related Cyber Scams
-
These two companies are favourites for spoofed emailsA quarterly report for cyber statistics has stated that two companies in...
-
Business Email Compromise: A Complete GuideEmail has become an inseparable part of any business. Sending invoices, making...
-
Why Web Application Firewall Is a Must In Your Security ArsenalIf your organization is cyber aware, you doubtless have procured some services...
-
Credentials Theft: A Case StudyCyber criminals keep creatively upping their game and this new phishing attack...
-
Major Data Breach of Government ComputersThe National Informatics Center (NIC) and the Ministy of Electronics & Information...
-
Look out for Covid-19 Related Cyber ScamsWhile regulations have lifted the restrictions of strict lockdowns, common sense and...