Blogs
Stay updated with the latest articles on technology, security, and digital transformation—designed to inform and inspire your business growth.
-
Blog23 August 2017Save billions by including cyber security within business strategyTechnology changes much faster than most business can keep up. The proliferation...
-
Blog21 August 2017Economic Impact of cyber-attacks on SMBs in 2017Cyber-criminals are now targeting Small and medium business enterprises to extort fees....
-
Blog17 August 2017CIO strategies for preventing new security breachesDigital transformation has ensured that cybersecurity is the biggest concern facing CIOs....
-
Blog13 August 2017Strategic risks of a cyber-attack in 2017!Open and digitally inter-connected technology platforms are shaping future of businesses. As...
-
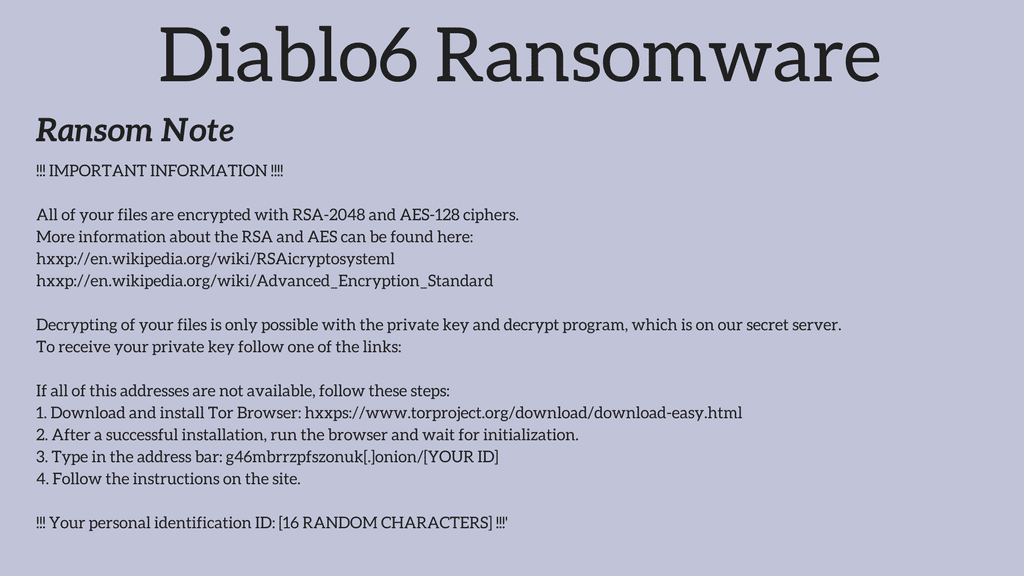
Blog11 August 2017Diablo6 – a variant of Locky RansomwareMany ransomwares continue to spread because email is ubiquitous and users are...
-
Blog8 August 2017How to invest smartly using cyber security metrices!In the hoax, usually companies end up spending blindly on the most...
-
Blog5 August 2017Which is the most apt vaccine for 2017 epidemic: Cyber-Attacks?With Internet, digitization, automation transformation taking center stage, cybersecurity turns up as...
-
Blog3 August 2017In 2017, to save yourself from hackers make DLP and cyber security walk hand in handEvery business today is on networked computer systems in order to achieve...
-
Blog26 July 2017Use your own Data wisely to detect an attack!Perennial, for a problem to exist that cyber-criminals areahead of security measures...
-
Reasons India Needs Better Cybersecurity in Banking
Banking in India is a very structured and regulated. Banks realize they're...
-
Buy Cloud Zimbra from the Logix eShop
We have the perfect solution on our eShop to help you boost...
-
Effective Endpoint Security
Endpoint security is a tricky subject, especially considering all the many devices...
-
Office365 Phishing Scam
When your go-to productivity applications start getting caught up in phishing scams,...
-
Microsoft Email Users Fall Prey to FedEx Phishing Emails
Microsoft email users seem to be repeatedly be targeted by one phishing...
-
Celsius Data Breach – Phishing Claims More Victims
Celsius, a crypto lending service, recently learned of a security break at...
-
Blog 10 June 2020 The Fake HR Email Phishing Scam -
Blog 2 June 2020 The Aramco-ONGC Fake Invoice Case -
Blog 29 May 2020 This New Phishing Scam Contains A Password Protected File -
Blog 24 May 2020 Logix Launches A Unique Service to Fight Against Invoice Fraud -
Blog 21 May 2020 The Phone Provider Phishing Scam – What is it and how to prevent it? -
Blog 15 May 2020 Office 365 and Cloud Zimbra | Hybrid Mail Solution
-
The Fake HR Email Phishing ScamWork from Home may have become tiresome; but don’t let your guard...
-
The Aramco-ONGC Fake Invoice CaseFake Invoices: The New Monster Indian Companies Have to Face? As we...
-
This New Phishing Scam Contains A Password Protected FileThe Password Protected File: Added Security or Phishing Attack? A new phishing...
-
Logix Launches A Unique Service to Fight Against Invoice FraudSecure Your Billing Process From Invoice Fraud Invoice Fraud is a type...
-
The Phone Provider Phishing Scam – What is it and how to prevent it?Don’t Trust Those Emails from Your Phone Providers In this age of...
-
Office 365 and Cloud Zimbra | Hybrid Mail SolutionLogix’s Hybrid Collaboration Solution: The Power of Two Giants at Your Disposal...