Blogs
Stay updated with the latest articles on technology, security, and digital transformation—designed to inform and inspire your business growth.
-
Blog3 July 2017Steps to stop targeted and advanced threatsTargeted attacks reap big rewards. Large organizations and institutions have faced a...
-
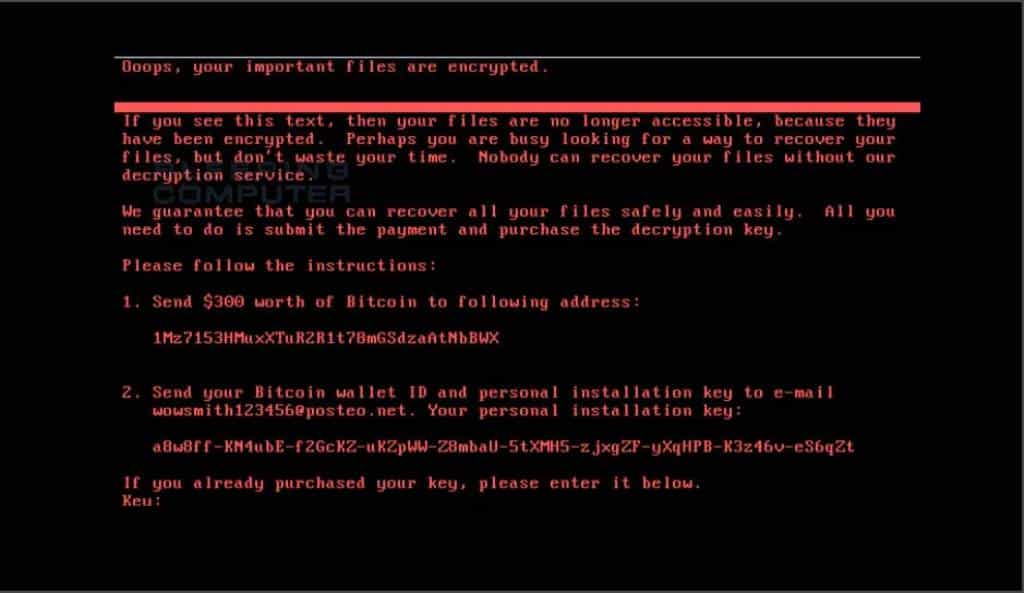
Blog28 June 2017Petya Ransomware is back to cause havocThe world suffered another wreaking nightmare on Tuesday with the attack of...
-
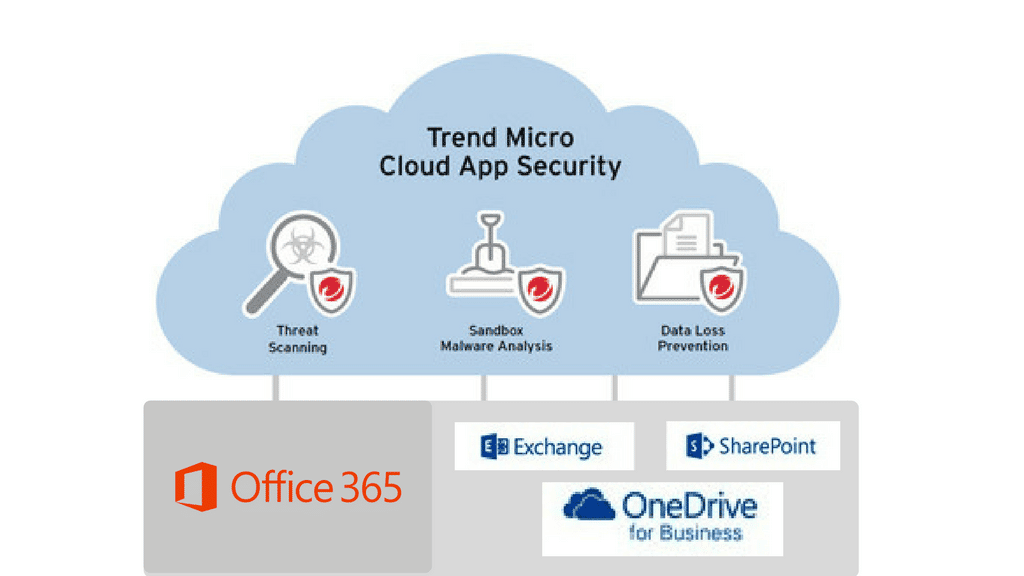
Blog19 June 2017How to protect your Cloud Files on Office 365Cloud computing has been around for quite some time now and it...
-
Blog15 June 2017How to select best email archiving solution for your company?A very important task is selecting an e-mail archiving product. Since archiving...
-
Blog12 June 2017Why do companies need Sandboxing?A sandbox gives you a chance to look into the future. It...
-
Blog5 June 2017Chinese Fireball Malware affects 250 Mn computers. India most affected.Possibly the largest malware infection operation in the history is on its...
-
Blog19 May 2017UIWIX Ransomware. The threat of WannaCry is not over yet.The evolved version of Wannacry ransomware; UIWIX Ransomware continues to shock the...
-
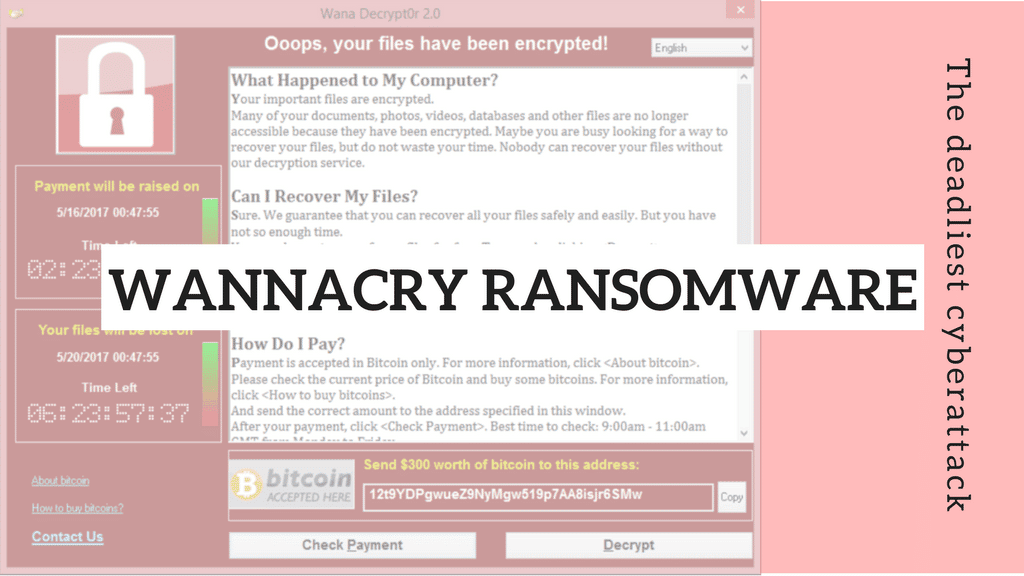
Blog17 May 2017WannaCry Ransomware: How it affected India? What could be done to keep safe? What is next?The Ransomware that shock the world started on 12th May as a...
-
Blog15 May 2017The latest global cyberattack – Wannacry Ransomware.On May 12th 2017, a ransomware of WannaCry or Wcry started spreading...
-
Blog2 May 2017Received a new job offer? Beware- Genuine or Fake?Scammers are on the rise with more and more fictitious job offers...
-
4 New Hacker Groups Target Microsoft Email Servers
After the focused attacks on Microsoft email servers by alleged state-sponsored hacking...
-
Microsoft Exchange Server Flaws Affect 30,000 Companies
A slow-burn cyber breach has been transpiring since January, only recently coming...
-
Hackers Target Government Officials Through Rogue Email ID
Several officials in the government were targeted for phishing through a rogue...
-
Getting a bonus is always good… unless it’s an advanced Bazar Trojan in disguise
Security researchers have found a deadly variant of a Bazar Trojan that...
-
Hosting Provider Phishing Scam
Cyber criminals will often use scare tactics to prod their victims into...
-
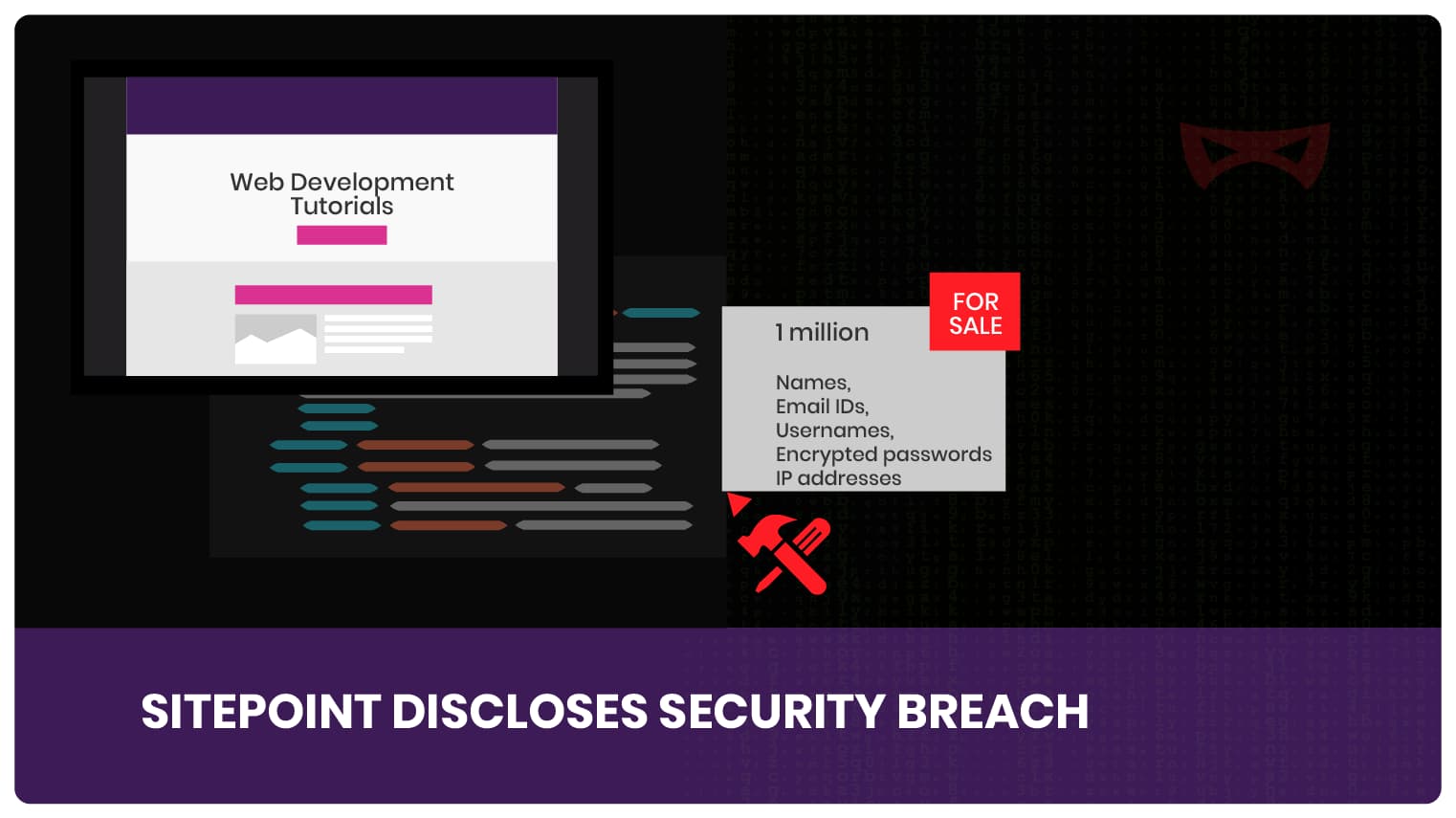
SitePoint Security Breach
SitePoint is an online portal which provides some great tutorials on web...
-
Blog 22 April 2020 Ransomware Strains In the News Again -
Blog 20 April 2020 Operation TA542 -
Blog 15 April 2020 Newsletter from Reserve Bank Information Technology Private Limited (ReBIT) on Cybersecurity -
Blog 13 April 2020 You’ve Won An Award: Is It Really Just Good News In That Celebratory Email? -
Blog 11 April 2020 Tree Sena: An Unfortunate Cybercrime Case That Affected A Noble Cause -
Blog 6 April 2020 Watch Out! Public Health Group Officials Being Imitated For Phishing Campaigns
-
Ransomware Strains In the News AgainTalos Incident Response Talks About New Ransomware Strains In a previous blog,...
-
Operation TA542Operation TA542: Emotet Resurfaces This botnet has been ping-ponging back and forth,...
-
Newsletter from Reserve Bank Information Technology Private Limited (ReBIT) on CybersecurityAn article shared by Mr. Nandkumar Saravade, CEO, ReBIT in Cyber Pulse...
-
You’ve Won An Award: Is It Really Just Good News In That Celebratory Email?Congratulations! You have won … a free phishing scam! Everybody loves to...
-
Tree Sena: An Unfortunate Cybercrime Case That Affected A Noble CauseTree Sena: A Sad Case of Identity Theft The scenario revolving around...
-
Watch Out! Public Health Group Officials Being Imitated For Phishing CampaignsPublic Health Group Officials Imitated for Sending Out Phishing Emails We have...