Blogs
Stay updated with the latest articles on technology, security, and digital transformation—designed to inform and inspire your business growth.
-
Blog24 March 2017Finding the appropriate Content Management System(CMS) for your OrganizationIn today’s market, you can find a Content Management System(CMS) at arm’s...
-
Blog20 March 2017Kirk Ransomware: Star trek themed malware!A new piece of ransomware has surfaced featuring star trek theme, named...
-
Blog16 March 2017Addressing the cyber security for your companyThere are multiple facets of cyber threats and so are multiple things...
-
Blog16 March 2017How to select web development company in India?Web has unprecedented increase in traffic. Businesses run from websites with the...
-
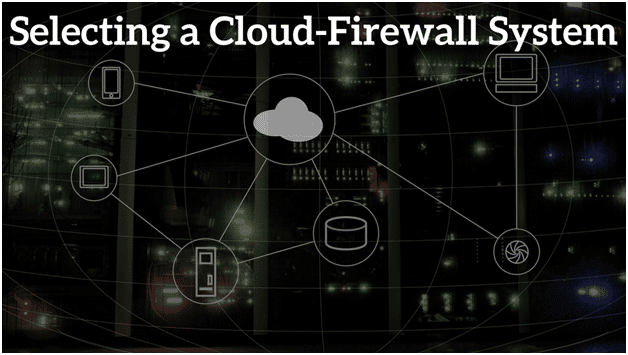
Blog9 March 2017Selecting A Cloud Firewall SystemCloud, the ease of use which comes with it and of course...
-
Blog8 March 2017Lawful Implementation of DLP Plan in IndiaData loss prevention (DLP) systems are crucial tools for the safeguards of...
-
Blog3 March 2017New target for hackers this year : Mac OSA second example of Malware targeting Mac OS has surfaced in the...
-
Blog2 March 2017The growing threat of GoldenEye Ransomware AttackThe latest version of Petya ransomware, GoldenEye, is attacking HR department with...
-
Blog27 February 2017Ransomware Spora: Everything you should know about itSpora is the latest ransomware trojan which is highly sophisticated in its...
-
Blog24 February 2017The Home Ministry’s website hacked on 2017 February 12On 12th February, 2017 the home ministry’s website got hacked. Attacks on...
-
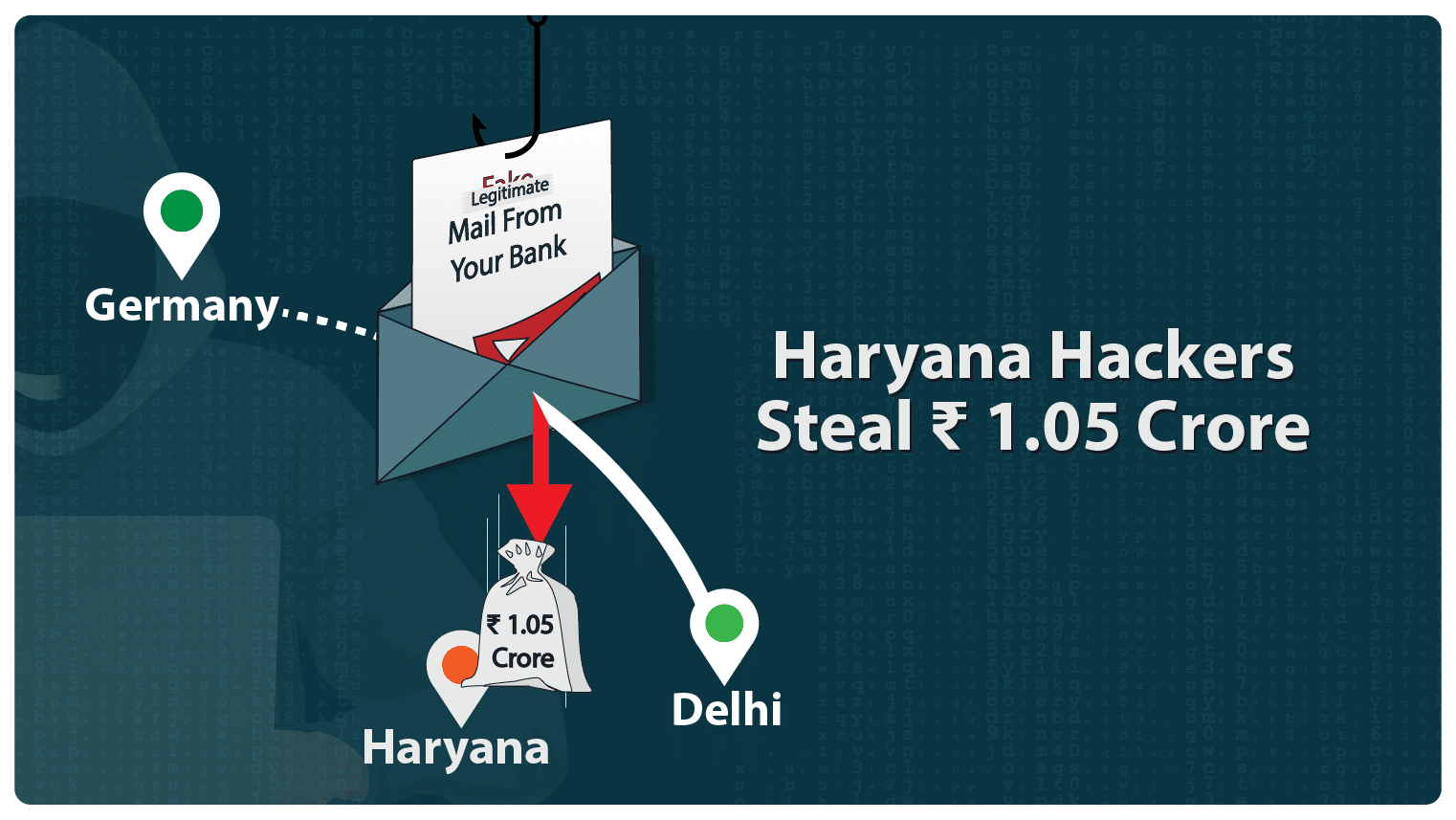
Haryana Hackers Steal INR 1 Crore
Haryana hackers defrauded ISGEC Heavy Engineering company and nicked an amount of...
-
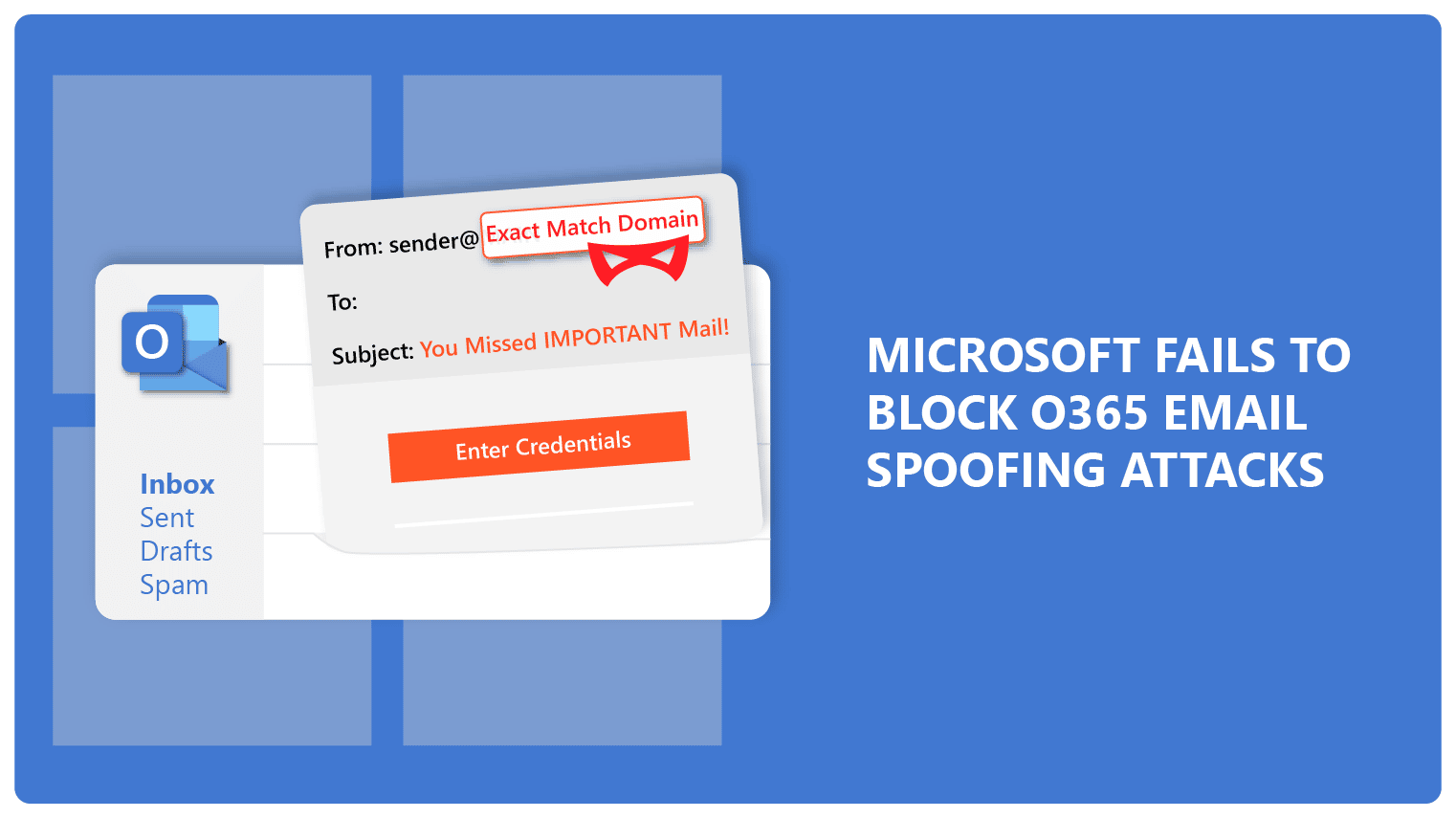
Microsoft Fails to Block O365 Email Spoofing Attacks
Microsoft is under the gun again for cyber fraud. 200 million+ users...
-
Webinar – Persistent Threats on Web-based Applications
Web-based critical applications are of utmost importance to organizations and your website is the gateway to the online world. However,...
-
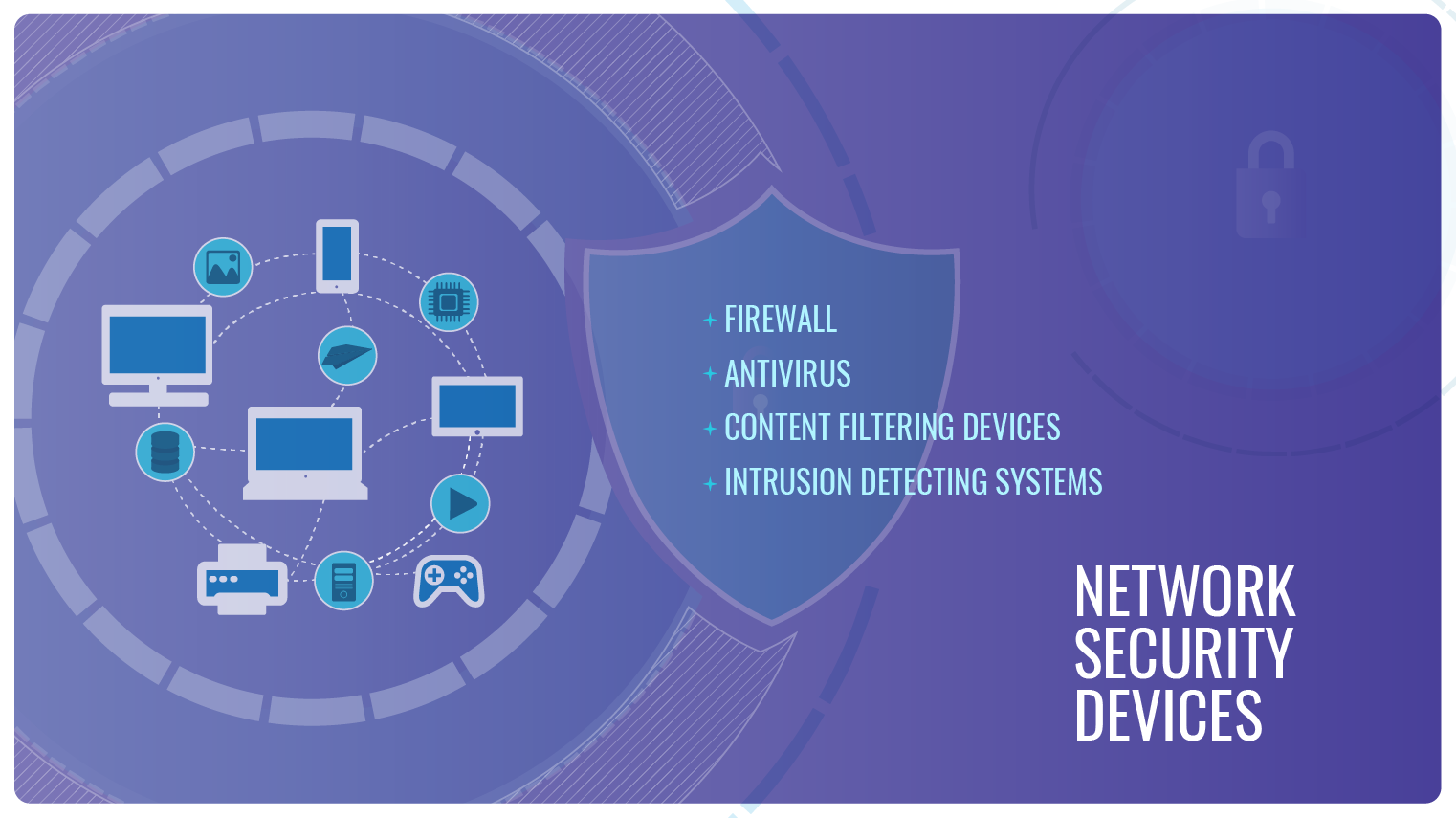
What are the types of Network Security Devices?
In a previous blog, we explored various concepts associated with network security....
-
Understanding Network Security
Communication to and from devices essentially happens via networks. That network can...
-
Features of Cisco Email ATP
Cisco provides one of the strongest email security solutions available today. In...
-
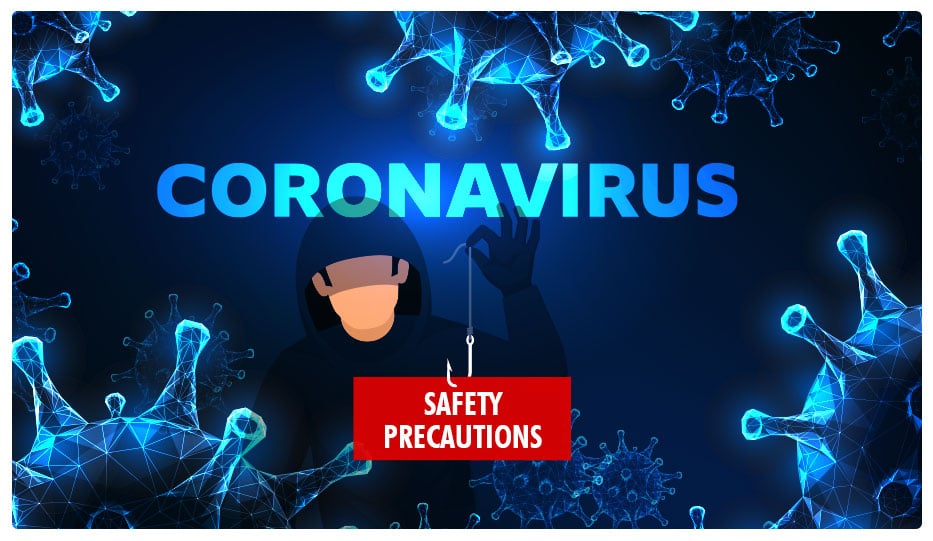
Blog 11 March 2020 COVID-19 Sparks A Series of Phishing Attacks -
Blog 2 March 2020 Fortinet Product Launch -
Blog 27 February 2020 Ransomware Delivers A Gut Punch To A Texas School District -
Blog 24 February 2020 Conversation Hijacking – The Latest Sneaky Phishing Technique -
Blog 20 February 2020 Using Artificial Intelligence To Battle Email Phishing -
Blog 17 February 2020 Cyber Attacks Take A Toll On Business
-
COVID-19 Sparks A Series of Phishing AttacksCybercriminals exploit the mass epidemic of COVID-19 Times are tough all over...
-
-
Ransomware Delivers A Gut Punch To A Texas School DistrictRansomware: The most damaging malware? The exact magnitude of a malware attack...
-
Conversation Hijacking – The Latest Sneaky Phishing TechniqueAll About Conversation Hijacking One of the biggest yet age-old perils of...
-
Using Artificial Intelligence To Battle Email PhishingArtificial Intelligence: A possible way to go when it comes to Email...
-
Cyber Attacks Take A Toll On BusinessCyber Attacks become the most feared threat to businesses If you are...