Blogs
Stay updated with the latest articles on technology, security, and digital transformation—designed to inform and inspire your business growth.
-
Blog12 December 2016Thinking About DdoS Attack Protection? 4 Reasons Why It’s Time To Stop!DDoS(Denial of Distributed Service) attack is a type of cyber attack that...
-
Blog7 December 2016What to expect new in cyber security trends in 2017In 2016 Spoofing, ransomware, phishing, and IoT-based DDoS attacks hit business and consumers....
-
Blog1 December 2016Logix Infosecurity : Microsoft office 365 partner in CoimbatoreIf you are looking for Microsoft office 365 partner in Coimbatore, your...
-
Blog1 December 2016Logix Infosecurity : Microsoft office 365 partner in AhmedabadIf you are looking for Microsoft office 365 partner in Ahmedabad, your...
-
Blog1 December 2016Logix Infosecurity : Microsoft office 365 partner in KolkataIf you are looking for Microsoft office 365 partner in Kolkata, your...
-
Blog30 November 2016[Infographic] Ransomware Attacks 2016 : Warning Act before you are the next VictimRansomware attacks continued to increase rapidly across 2016.According to Beazley Report, trend...
-
Blog28 November 20168 Security Questions you should ask your Web Hosting ProvidersWhen you face security challenges with your Web hosting it can be...
-
Blog25 November 20165 Preventive Tips to fight against MalvertisingCyber criminals are becoming quite innovative these days. They are dedicatedly inventive...
-
Blog19 November 2016Why messaging and collaboration tools are most valuable enterprise apps?According to Adobe 2016 Mobile Apps Report Messaging and collaboration applications are the...
-
Blog16 November 2016BFSI again scores high for email security threats and cybercrimes in 2016BFSI Sector has always been favorite of all hackers and attackers. BFSI...
-
These two companies are favourites for spoofed emails
A quarterly report for cyber statistics has stated that two companies in...
-
Business Email Compromise: A Complete Guide
Email has become an inseparable part of any business. Sending invoices, making...
-
Why Web Application Firewall Is a Must In Your Security Arsenal
If your organization is cyber aware, you doubtless have procured some services...
-
Credentials Theft: A Case Study
Cyber criminals keep creatively upping their game and this new phishing attack...
-
Grow Your Business with the Logix Partnership Program
We believe stronger networks are key for the overall growth of business....
-
Major Data Breach of Government Computers
The National Informatics Center (NIC) and the Ministy of Electronics & Information...
-
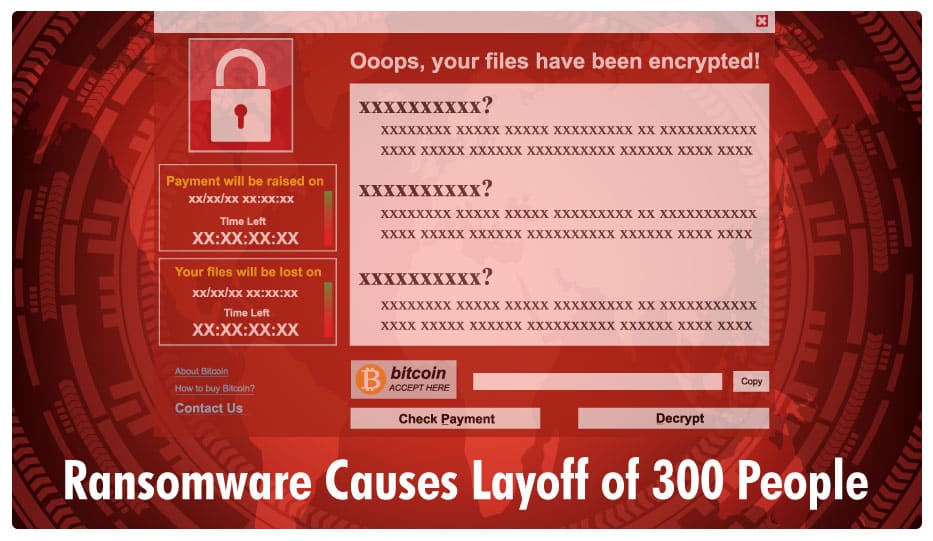
Blog 30 December 2019 Ransomware Causes 300 People To Lose Their Jobs -
Blog 25 December 2019 Emotet botnet malware hidden within fake Christmas party invites -
Blog 23 December 2019 Microsoft Report on Cleverest Phishing Tactics -
Blog 19 December 2019 Best Practices For Online Security -
Blog 16 December 2019 Ukraine Targeted by a Russian APT Hacker Team -
Blog 12 December 2019 Defence Ministry Targeted For Phishing
-
Ransomware Causes 300 People To Lose Their JobsRansomware Forces An Organization To Let Go Of 300 Employees Ransomware has...
-
Emotet botnet malware hidden within fake Christmas party invitesBeware: Your Christmas party emails could be infected with malware Nobody likes...
-
Microsoft Report on Cleverest Phishing TacticsMicrosoft Reports on the Cleverest Phishing Tactics of 2019 While for individuals...
-
Best Practices For Online SecuritySecurity Practices for Your Business — How many can you check off...
-
Ukraine Targeted by a Russian APT Hacker TeamRussian APT Hacker Team Strikes Out The Military and the Government are...
-
Defence Ministry Targeted For PhishingWarning Issued for Defence Personnel The defence ministry has issued an emergency...