Blogs
Stay updated with the latest articles on technology, security, and digital transformation—designed to inform and inspire your business growth.
-
Blog30 September 2016Gain Office 365 Security through multi factor authenticationSecurity being a biggest concern in cloud, lets look at how can...
-
Blog29 September 20165 Reasons why you should consider Microsoft Office 365 over Hosted ExchangePicking the right cloud answer for your business email can be hard,...
-
Blog29 September 2016Logix Infosecurity : Microsoft Office 365 reseller in MumbaiAre you looking for Microsoft Office 365 reseller in Mumbai? Your search ends...
-
Blog28 September 2016Logix Infosecurity : Microsoft office 365 partner in MumbaiIf you are looking for Microsoft office 365 partner in Mumbai, your...
-
Blog22 September 2016Email phishing attacks: Know before you click phishing websiteEmail Phishing attacks rose in the Christmas 2015 season, and have continued...
-
Blog21 September 2016CryptoJoker Ransomware: 4 Life-saving tips to protect your filesCryptojoker ransomware is another name to the ransomware list. 2016 is shaping...
-
Blog18 September 2016Email security statistics 2016 Know before you are next victimIs Email Security a concern for you? If not read the facts...
-
Blog15 September 2016Bingo !! Logix Infosecurity is recognized as best Microsoft Cloud Service Provider in IndiaWe are absolutely thrilled.We are recognized as the Best Microsoft Cloud Service...
-
Blog12 September 2016Be-aware : 20+ Email spoofing cases in India in 2016 may shock you.Email spoofing attacks in business is growing exponentially in India. There has...
-
Blog10 September 2016Ransomware attacked 180 Indian companies : shocked by the news?Read a news on Economic Times that Ransomware attacked 180 Indian Companies. Ransomware,...
-
The Value of Mass Email Marketing Tools
What is the value of Mass Email Marketing? If you’re a business...
-
Fraudster impersonated a prominent bank’s email domain to commit fraud
Bank's Email Domains Impersonated to Commit Fraud Against Prothious Engineering Services An...
-
The Threat Of Business Email Compromise
Business Email Compromise Becomes the Most Common Cyber Attack Webinars are part...
-
Tax Accounting Software Spoofed
Tax Accounting Software Misused for Phishing Scam, CEOs Under Threat A multi-national...
-
9 Email Threats You Should Prevent
Why worry about Email Security? Email is the entry point for a...
-
The Free Covid Testing Phishing Scam
A Major Phishing Campaign Is Coming Your Way, Promising Free Covid Testing...
-
Blog 21 October 2019 The ABCs of Malware – An informative Blog Series (Part 3 of 3) -
Blog 18 October 2019 The ABCs of Malware – An informative Blog Series (Part 2 of 3) -
Blog 14 October 2019 The ABCs of Malware – An informative Blog Series (Part 1 of 3) -
Blog 11 October 2019 Amazon Prime Phishing Scam – Don’t fall for the “Account Frozen” Act! -
Blog 7 October 2019 Vloggers Under The Threat Of Phishing -
Blog 3 October 2019 The two branches of Phishing: Vishing and Smishing
-
The ABCs of Malware – An informative Blog Series (Part 3 of 3)All About Malware – Safeguarding Against Malware This is Part Three of...
-
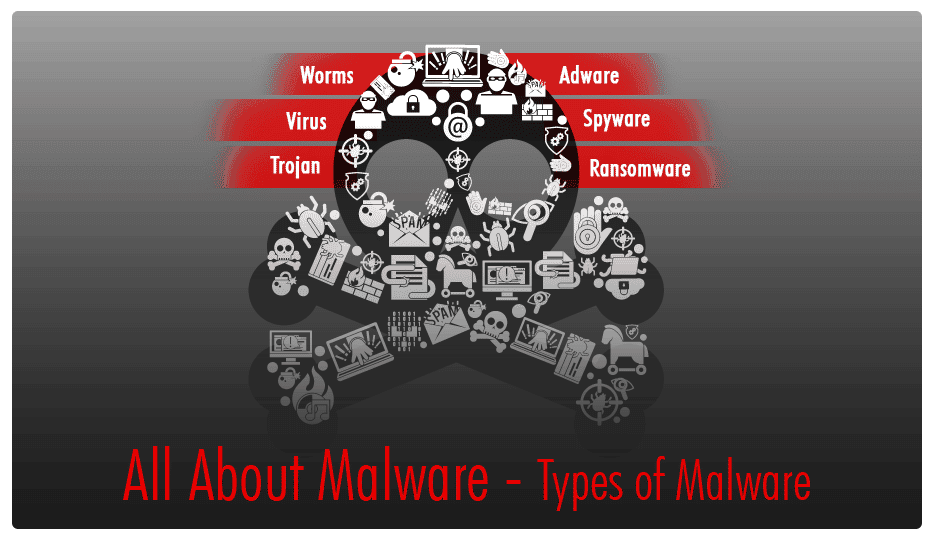
The ABCs of Malware – An informative Blog Series (Part 2 of 3)All About Malware – Types of Malware This is Part Two of the...
-
The ABCs of Malware – An informative Blog Series (Part 1 of 3)All About Malware – Introduction & Working This is Part One of...
-
Amazon Prime Phishing Scam – Don’t fall for the “Account Frozen” Act!Don’t Panic Online Shoppers, Amazon Prime is NOT Locked If you’re an...
-
Vloggers Under The Threat Of PhishingVloggers- the latest victims of phishing attacks Phishing attacks are not only...
-
The two branches of Phishing: Vishing and SmishingPhishing gets two new neighbours, and they are just as deadly Phishing,...