Blogs
Stay updated with the latest articles on technology, security, and digital transformation—designed to inform and inspire your business growth.
-
Emotet botnet malware hidden within fake Christmas party invites
Beware: Your Christmas party emails could be infected with malware Nobody likes...
-
Microsoft Report on Cleverest Phishing Tactics
Microsoft Reports on the Cleverest Phishing Tactics of 2019 While for individuals...
-
Best Practices For Online Security
Security Practices for Your Business — How many can you check off...
-
Ukraine Targeted by a Russian APT Hacker Team
Russian APT Hacker Team Strikes Out The Military and the Government are...
-
Defence Ministry Targeted For Phishing
Warning Issued for Defence Personnel The defence ministry has issued an emergency...
-
Celebrating 20 Glorious Years of Logix…
We cherish this journey of 20 years which started with a very humble...
-
Blog 14 January 2019 4 things you must know about Cyber Security in the era of IoT -
Blog 10 January 2019 Chinese hackers swindles Rs. 130 crore from an Indian arm of an Italian company -
Blog 4 January 2019 Aadhar Card Data Leak calls for better cyber security! -
Blog 27 December 2018 5 cybersecurity question every CIO must ask in 2019 -
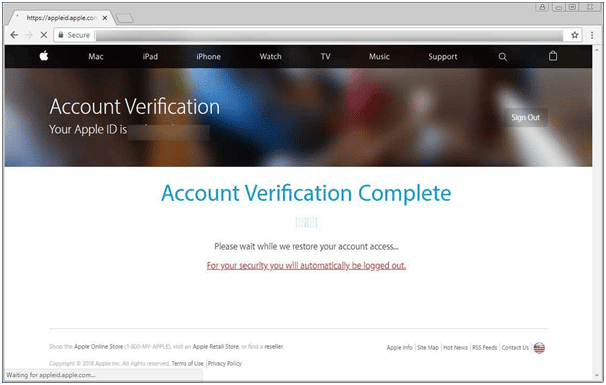
Blog 22 December 2018 Widespread Apple ID Phishing Attack Pretends to be App Store Receipts -
Blog 20 December 2018 Are the e-commerce sites cyber-safe?
-
4 things you must know about Cyber Security in the era of IoTCyber Security in the era of Internet-of-things is a changing paradigm. According...
-
Chinese hackers swindles Rs. 130 crore from an Indian arm of an Italian companyA Chinese hackers team stole 18.3 million dollars (Rs. 130 Crore) from the...
-
Aadhar Card Data Leak calls for better cyber security!Aadhar Card data of 130 million as well as bank account details have...
-
5 cybersecurity question every CIO must ask in 2019There has been a far greater responsibility on the Chief Information Officers(CIOs)...
-
Widespread Apple ID Phishing Attack Pretends to be App Store ReceiptsThis is big, the Apple-ID which managed to stay away from compromises...
-
Are the e-commerce sites cyber-safe?Can there be someone else in your shopping cart? Well, the scenario...