Blogs
Stay updated with the latest articles on technology, security, and digital transformation—designed to inform and inspire your business growth.
-
Blog19 December 2024Understanding Identity and Access Management (IAM)Data security and access control are paramount for organizations of all sizes....
-
Blog18 December 2024India Ranks Third Globally for Phishing AttacksAccording to the latest report by cybersecurity firm Zscaler, India now ranks...
-
Blog18 December 2024Endpoint Detection and Response for Protecting Your Organization from Elusive ThreatsTraditional security solutions often fall short against sophisticated attacks that infiltrate endpoints...
-
Blog16 December 2024Strengthening Cybersecurity with the Essential Eight StrategiesWith cybercriminals targeting critical infrastructure and third-party vendors, it's imperative for enterprises...
-
Blog16 December 2024Spotting and Preventing Phishing Scams in HospitalityCybersecurity threats are around every corner today, especially for industries like hospitality...
-
Blog16 December 2024The Imperative of Cybersecurity for Business Resilience: A Call to ActionCybercrime tactics such as phishing and social engineering are reaching dangerous levels....
-
Blog12 December 2024A Sneaky Twist on Phishing: BazarCall Attacks Google FormsA new type of BazarCall attack is causing trouble by using a...
-
Blog9 December 2024Defend Your Data: The Power of Acronis Endpoint BackupRansomware attacks can occur at any time, potentially leading to the loss...
-
Blog6 December 2024Streamline Your Data Protection with Acronis Cloud to Cloud BackupAcronis Cyber Protect Cloud is your comprehensive solution for seamless and secure...
-
Blog6 December 2024Maximize Data Protection with Acronis Backup for Microsoft 365Microsoft offers a robust infrastructure, but it's crucial to recognize that data...
-
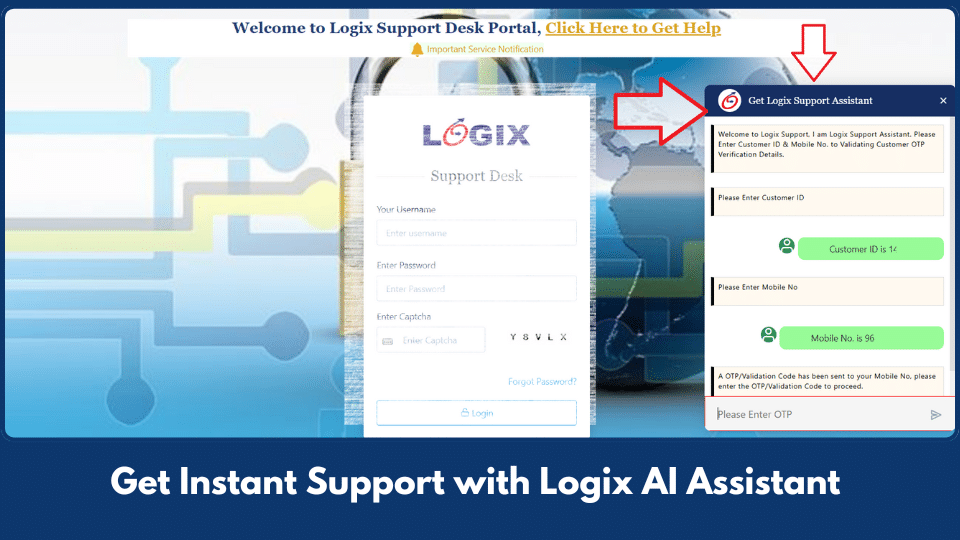
Get instant support with Logix AI assistant
Introducing Logix Support Assistant bot Dear Valued Customer, We're excited to introduce...
-
Microsoft announces phishing protection for Teams
As cyber threats evolve, so must your organization’s defenses. Microsoft has taken...
-
Barracuda Email Archival Solves Outlook’s Storage Problem
Emails are the backbone of business communication, but as organizations grow, so...
-
Are Cyrillic Characters a Cybersecurity Risk?
A recent Facebook post shows two web addresses that, at first glance,...
-
Why Businesses Must Prioritize Phishing Protection
Cybercriminals are getting smarter, and phishing attacks have become one of the...
-
MS Business Premium – Your complete office on the cloud
Microsoft 365 Business Premium offers a comprehensive suite of productivity tools and...
-
Blog 21 February 2025 Multi-Factor Authentication (MFA) for Office 365 -
Blog 11 February 2025 Workplace Cyber Security with Check Point Harmony -
Blog 11 February 2025 Why Phishing-Resistant MFA Is Now a Necessity for Cybersecurity -
Blog 8 February 2025 QR Code Phishing Attacks Doubled in India -
Blog 8 February 2025 How Simulated Phishing Keeps Employees Sharp Against Cyber Threats -
Blog 8 February 2025 Logix Internal Sales Meet 2024
-
Multi-Factor Authentication (MFA) for Office 365In today's digital age, securing your accounts is more important than ever....
-
Workplace Cyber Security with Check Point HarmonyWith more and more organisations picking Office 365 and Google for their...
-
Why Phishing-Resistant MFA Is Now a Necessity for CybersecurityThe rapidly evolving cyber threat landscape has made one thing abundantly clear:...
-
QR Code Phishing Attacks Doubled in Indiain recent years, India has witnessed a significant increase in digital payment...
-
How Simulated Phishing Keeps Employees Sharp Against Cyber ThreatsOne of the most common and dangerous types of cyberattacks is phishing....
-
Logix Internal Sales Meet 2024The Logix Internal Sales Meet 2024 focused on new product innovations, sales...