Blogs
Stay updated with the latest articles on technology, security, and digital transformation—designed to inform and inspire your business growth.
-
Is implementing DMARC a cake walk or a tedious job?
It is a cliché in IT industry for people to judge software...
-
FlawedAmmyy RAT being delivered via TA505 email spam campaigns
Always be cautious while opening email attachments. Recently, hackers have been sending...
-
Emotet Malware spreading extensively via Microsoft Documents in emails
Hackers are trying to deliver Emotet malware by attaching it to Microsoft...
-
Cloud Technology has brought in a paradigm shift in Storing Data
Cloud Computing has flourished enormously over the past few years. It has...
-
Indian BFSI Sector needs to be prepared for upcoming data protection laws
The increase in financial crimes is not only a threat to BFSI...
-
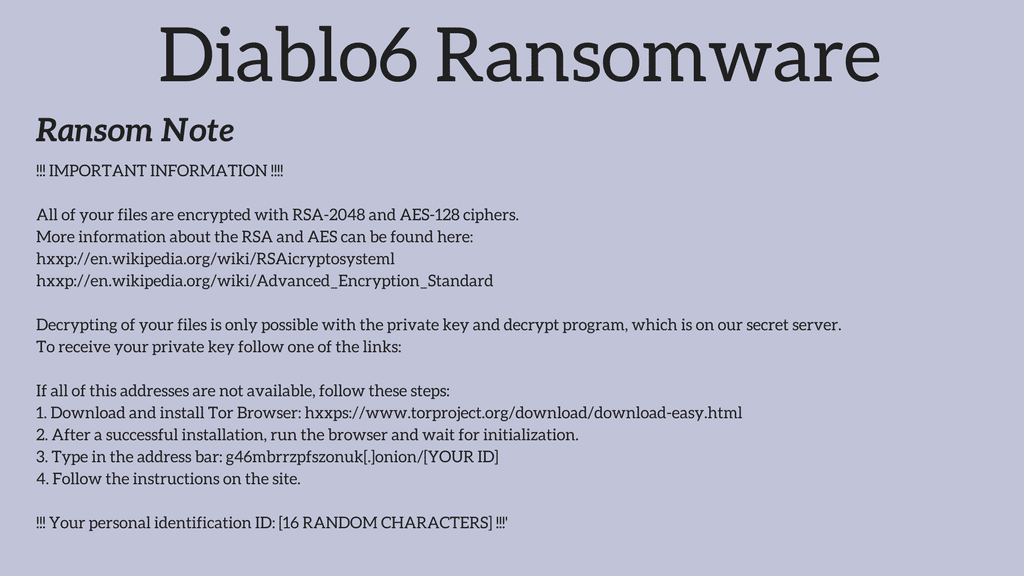
Blog 11 August 2017 Diablo6 – a variant of Locky Ransomware -
Blog 8 August 2017 How to invest smartly using cyber security metrices! -
Blog 5 August 2017 Which is the most apt vaccine for 2017 epidemic: Cyber-Attacks? -
Blog 3 August 2017 In 2017, to save yourself from hackers make DLP and cyber security walk hand in hand -
Blog 31 July 2017 [Infographic] Ransomware Victims Paid more than $25 Million in the last couple of years -
Blog 26 July 2017 Use your own Data wisely to detect an attack!
-
Diablo6 – a variant of Locky RansomwareMany ransomwares continue to spread because email is ubiquitous and users are...
-
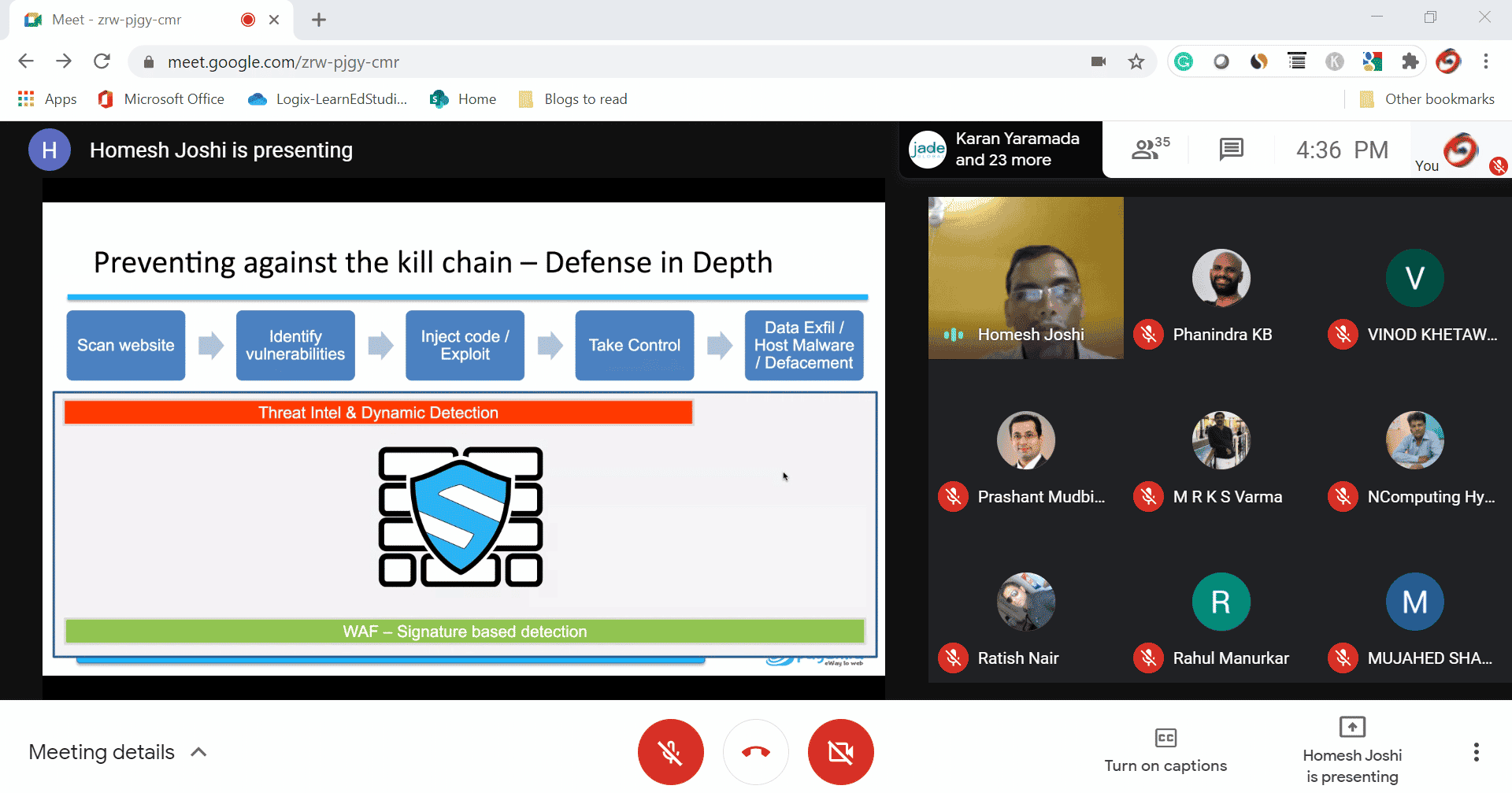
How to invest smartly using cyber security metrices!In the hoax, usually companies end up spending blindly on the most...
-
Which is the most apt vaccine for 2017 epidemic: Cyber-Attacks?With Internet, digitization, automation transformation taking center stage, cybersecurity turns up as...
-
In 2017, to save yourself from hackers make DLP and cyber security walk hand in handEvery business today is on networked computer systems in order to achieve...
-
Use your own Data wisely to detect an attack!Perennial, for a problem to exist that cyber-criminals areahead of security measures...


![[Infographic] Ransomware Victims Paid more than $25 Million in the last couple of years](https://dev.logix.in/wp-content/plugins/elementor/assets/images/placeholder.png)