Blogs
Stay updated with the latest articles on technology, security, and digital transformation—designed to inform and inspire your business growth.
-
ODNS would be an internet security breakthrough
The DNS is essentially a phonebook for the Internet’s domain names. When...
-
Cyber criminals have discovered a new way to bypass Office 365 Safe Links
Microsoft’s Advanced Threat Protection (ATP) includes a feature called Safe Links. Office...
-
Data hacked during EPFO-Aadhar seeding
Cyber criminals seem to have hacked the EPFO data which holds information...
-
Smartly defining RPO and RTO for Disaster Recovery Plans
Recovery Point Objective (RPO) and Recovery Time Objective (RTO) are 2 most...
-
Formbook Malware spreading widely by clicking Microsoft URL shortcut files in your emails
Be careful when you receive attachments to an email, it can be...
-
CIOs must run a customer centric business
It is high time for CIOs to run a customer centric business....
-
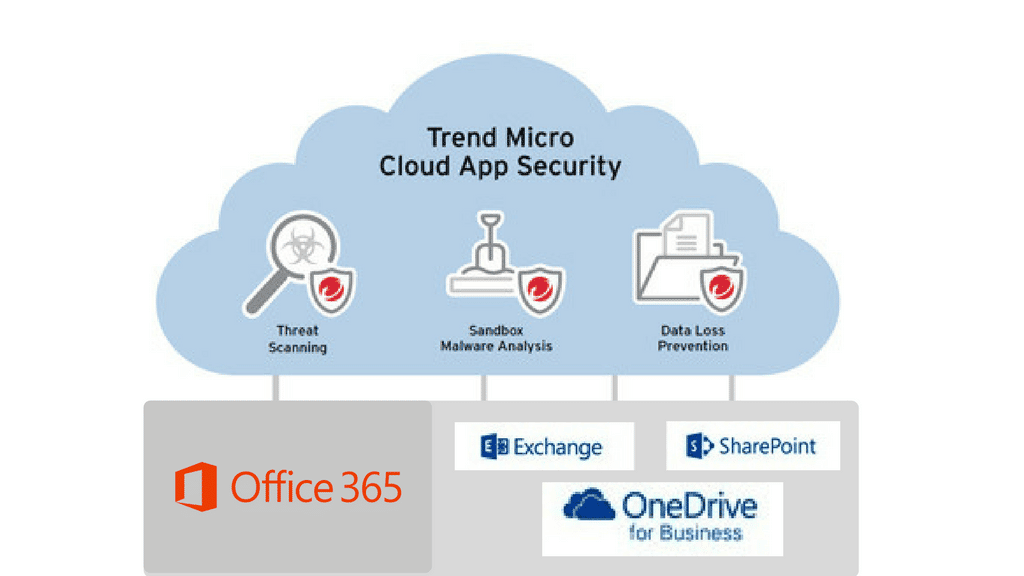
Blog 19 June 2017 How to protect your Cloud Files on Office 365 -
Blog 15 June 2017 How to select best email archiving solution for your company? -
Blog 12 June 2017 Why do companies need Sandboxing? -
Blog 5 June 2017 Chinese Fireball Malware affects 250 Mn computers. India most affected. -
Blog 19 May 2017 UIWIX Ransomware. The threat of WannaCry is not over yet. -
Blog 17 May 2017 WannaCry Ransomware: How it affected India? What could be done to keep safe? What is next?
-
How to protect your Cloud Files on Office 365Cloud computing has been around for quite some time now and it...
-
How to select best email archiving solution for your company?A very important task is selecting an e-mail archiving product. Since archiving...
-
-
Chinese Fireball Malware affects 250 Mn computers. India most affected.Possibly the largest malware infection operation in the history is on its...
-
UIWIX Ransomware. The threat of WannaCry is not over yet.The evolved version of Wannacry ransomware; UIWIX Ransomware continues to shock the...
-
WannaCry Ransomware: How it affected India? What could be done to keep safe? What is next?The Ransomware that shock the world started on 12th May as a...