Blogs
Stay updated with the latest articles on technology, security, and digital transformation—designed to inform and inspire your business growth.
-
Indian Government needs to give cyber security an equal priority to border security
Digital India is no more a dream but carving into an absolute...
-
Rarog – A cryptomining Trojan is out in the wild
A malware family Rarog is out in the internet and being excessively...
-
Private Cloud vs Public Cloud. Making the perfect choice!
Embracing cloud technology is no longer a choice but an inevitable business...
-
Slingshot, an APT Malware making its way through routers in the Network
An APT (Advanced Persistent Threat) malware, Slingshot, attacks victims by entering via...
-
Microsoft Office 365 provides new Advanced Security Features
Microsoft Office 365 is widely popular work office suite, among the SMBs....
-
Is blockchain the alchemy to DDoS attacks?
DDoS(Denial of Distributed Service) attack is a type of cyber attack that...
-
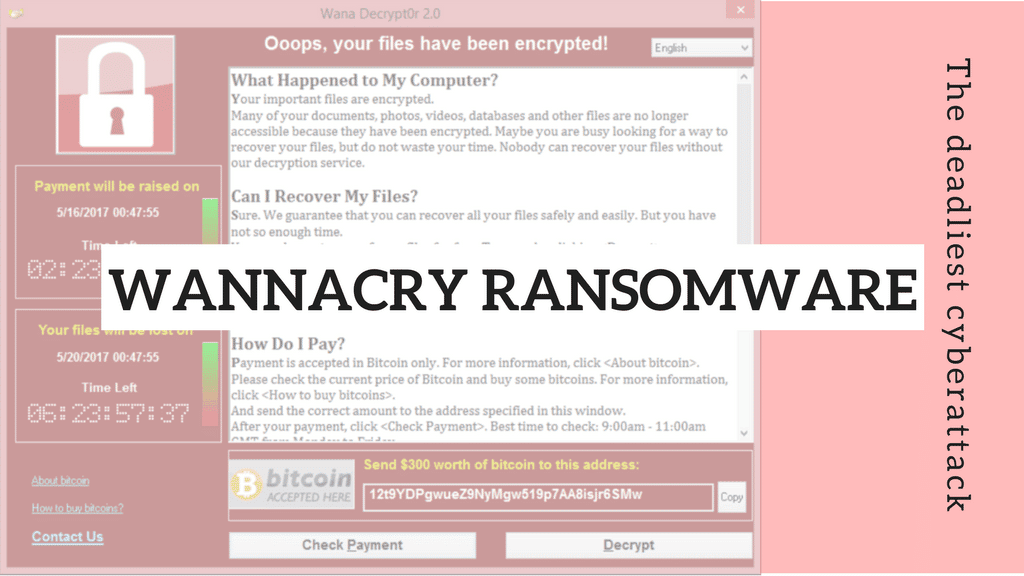
Blog 15 May 2017 The latest global cyberattack – Wannacry Ransomware. -
Blog 2 May 2017 Received a new job offer? Beware- Genuine or Fake? -
Blog 28 April 2017 Which is the best choice for your organization- Shared or Dedicated web hosting? -
Blog 10 April 2017 Why do companies need responsive web design? -
Blog 10 April 2017 Matrix Ransomware: Spreading to PCs through Malicious Shortcuts -
Blog 9 April 2017 What is Penetration Testing? And Why is it important for your organization?
-
The latest global cyberattack – Wannacry Ransomware.On May 12th 2017, a ransomware of WannaCry or Wcry started spreading...
-
Received a new job offer? Beware- Genuine or Fake?Scammers are on the rise with more and more fictitious job offers...
-
Which is the best choice for your organization- Shared or Dedicated web hosting?Running a mid-sized business; choosing between a shared and dedicated web hosting...
-
Why do companies need responsive web design?Responsive web design is an approach to creating web sites which can...
-
Matrix Ransomware: Spreading to PCs through Malicious ShortcutsThe latest addition to the growing threat of ransomware is the Matrix...
-
What is Penetration Testing? And Why is it important for your organization?Penetration testing or commonly known as pen testing is another important way...